Beyond firewalls – addressing cybersecurity blind spots
By Victor Ng | Mar 2, 2026
Where are financial fraud and AML regulations heading in S E...
By Victor Ng | Feb 10, 2026
How AI is reshaping dating in Asia
By CybersecAsia editors | Feb 9, 2026
Emerging third-party cyber risks via agentic AI
By Victor Ng | Feb 3, 2026
Rethinking customer identity for financial cybersecurity
By Victor Ng | Jan 27, 2026
SECURITY NEWS
Global data theft campaign exploits misconfigured cloud portals to harvest massive troves of corporate records
Mar 12, 2026
Attackers abuse guest access on CRM portals, chaining server actions and bypassing query limits to extract sensitive organizational data worldwide
-

-

-

Building trust in the age of AI
Mar 10, 2026
EXPERT OPINIONS
How escalating geopolitical tensions are expanding the cybersecurity frontline
Mar 5, 2026
As geopolitical tensions rise and conflicts increasingly play out both on the ground and online, the line between national security and business risk is quickly fading.
-

Redefining the future of cyber insurance
Mar 4, 2026
-

-

TIPS
When AI adoption outpaces security, organizations struggle for collective safety
Mar 12, 2026
Skyrocketing AI integration can expose serious gaps in data protection, operational resilience, and responsible use — requiring shared accountability and continuous oversight.
















CLOUD SECURITY
HOSTWAY gains 73% operational efficiency for private cloud operations
Oct 2, 2025
With NetApp storage solutions, the Korean managed cloud service provider offers a lean, intelligent architecture, powered by automation and an Infrastructure-as-Code approach.
Are Your Business Secrets Really Secret and Secure?
Jan 21, 2025
“Bump in the night”: What’s next?
Sep 26, 2024
INFOGRAPHICS
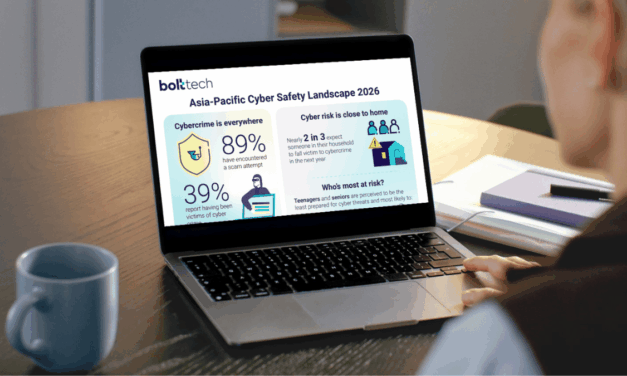
Asia Pacific Cyber Safety Landscape 2026
Mar 6, 2026
Global insurtech bolttech's new research examines the cyber protection gap across Asia Pacific’s emerging and developed markets.
-

2026 State of Security and Identity Report
Mar 5, 2026
Cyber Intelligence
LatestW3LL-oiled machine: report uncovers covert BEC phishing empire targeting Microsoft 365
By CybersecAsia editors and webmaster webmaster | Sep 7, 2023
A new threat report “W3LL DONE: HIDDEN PHISHING ECOSYSTEM DRIVING BEC ATTACKS” has detailed the operations of W3LL, a threat actor behind a phishing empire that has remained largely unknown until now.
-

-

-

Making cyber-resilience part of your organization’s balance sheet
By Victor Ng | Apr 26, 2022
Cyber Warfare
LatestHow escalating geopolitical tensions are expanding the cybersecurity frontline
By Ismael Valenzuela, VP, Threat Intelligence Research, Arctic Wolf | Mar 5, 2026
As geopolitical tensions rise and conflicts increasingly play out both on the ground and online, the line between national security and business risk is quickly fading.
-

-

-

Ransomware still the #1 cyber threat: report
By CybersecAsia editors | Jan 30, 2023
MOST READ
WhatsApp group chat vulnerability hack thwarted
Researchers had discovered in August a group-chat flaw where a malicious message could crash WhatsApp group users’ devices. A...
Nine DevSecOps secret scanning tools to keep the bad guys at bay
With the secrets of over 2m corporations already leaked, it is time to mandate action to plug the preventable gaps
sponsors-RCA
CybersecAsia Readers’ Choice Awards Ceremony Teaser


Fireside Chat


WHAT’S NEXT
WHAT'S NEXT |
|---|
Webinars: |
|
⚫ June 9, 2021: Prospect Webinar |
|
⚫June 9-10, 2021: Partner Webinars – BlackBerry Gateway, Optics 3.0 |
Newsletters: |
|
⚫June 2, 2021: Partner Newsletter – Gateway |
|
⚫June 8, 2021Customer Newsletter |