Minimizing false positives in digital payment
By Victor Ng | Oct 15, 2024
In 2024 and beyond, is Cybersecurity Awareness Month obsolet...
By Victor Ng | Oct 8, 2024
Cyber risks vs productivity – AI dichotomy in the workplace...
By Victor Ng | Oct 2, 2024
The tough conversations about cybersecurity
By Victor Ng | Oct 2, 2024
SECURITY NEWS
Staying Ahead – RSA Conference
By RSA Conference | Jun 12, 2019
Amrin Amin, Senior Parliamentary Secretary (SPS), Ministry of Home Affairs & Ministry of Health Proliferation of digital...
-

Cybersecurity Futures 2025: Insights and Findings for RSAC
By RSA Conference | May 12, 2019
-

-

The New Why of Cybersecurity
By RSA Conference | Mar 12, 2019
-

Think and act like a hacker to protect your company’s assets
By RSA Conference | Jan 12, 2019
EXPERT OPINIONS
Staying Ahead – RSA Conference
By RSA Conference | Jun 12, 2019
Amrin Amin, Senior Parliamentary Secretary (SPS), Ministry of Home Affairs & Ministry of Health Proliferation of digital...
-

Cybersecurity Futures 2025: Insights and Findings for RSAC
By RSA Conference | May 12, 2019
-

-

The New Why of Cybersecurity
By RSA Conference | Mar 12, 2019
-

Think and act like a hacker to protect your company’s assets
By RSA Conference | Jan 12, 2019
TIPS
Staying Ahead – RSA Conference
By RSA Conference | Jun 12, 2019
Amrin Amin, Senior Parliamentary Secretary (SPS), Ministry of Home Affairs & Ministry of Health Proliferation of digital...
-

Cybersecurity Futures 2025: Insights and Findings for RSAC
By RSA Conference | May 12, 2019
-

-

The New Why of Cybersecurity
By RSA Conference | Mar 12, 2019
-

Think and act like a hacker to protect your company’s assets
By RSA Conference | Jan 12, 2019
Staying Ahead – RSA Conference
By RSA Conference | Jun 12, 2019
Cybersecurity Futures 2025: Insights and Findings for RSAC
By RSA Conference | May 12, 2019
The New Why of Cybersecurity
By RSA Conference | Mar 12, 2019
Infographics

Verizon 2024 Mobile Security Index Infographic

Acronis Cyberthreats Report H1 2024 Infographic

Verizon 2024 Data Breach Investigations ... Infographic

2024 Global Threat Report Infographic




APJ 2023 Direction of Technology Report Infographic

Trust and collaboration to fight fraud i... Infographic
Before and After: How Exposure Managemen... Infographic


State of Cybersecurity in ASEAN 2023 Infographic

Use of phishing kits surged by 25% in 20... Infographic
2023 Global State of Cybersecurity Infographic

Unit 42 Cloud Threat Report Infographic

Know your adversaries Infographic
Usher in the Year of the Rabbit, not the... Infographic

APAC cybersecurity predictions 2023 Infographic

#ShopSafe tips for your customers this h... Infographic

Infographics: 6 steps to defend against ... Infographic
10 best practices to turbo boost cyberse... Infographic
Tips: Ways to implement risk-based vulne... Infographic
2022 State of Access Control Infographic

Anatomy of a multiple-gang attack Infographic

Infographics: Cyber Threat Landscape in ... Infographic

Ransomware: true cost to business 2022 Infographic

Q1 2022 ransomware update Infographic

Simpler and stronger multi-device passwo... Infographic

Charity scams in 2022 Infographic

Ransomware gold rush Infographic

Balancing risk and reward Infographic

State of Cybersecurity Report ASEAN 2022 Infographic
10 trends that will shape the fraud land... Infographic

Top trends in data protection for 2022 Infographic




Fighting financial crimes in 2022 Infographic

2022: How APAC is preparing for a new th... Infographic

APAC security predictions 2022 Infographic

Global Security Attitude Survey 2021 Infographic


Impact of pandemic on 2021 holiday shopp... Infographic

Ransomware attackers don’t take holidays... Infographic

Redefining trust and risk in APAC Infographic

Patch management challenges Infographic
2021 State of PKI Automation in APAC Infographic

Asia Pacific SMBs prepare for digital de... Infographic

Rethink your SMS approach Infographic

How companies tackle trade compliance Infographic

Security risks of network overprovisioni... Infographic

2021 Global Incident Response Threat Rep... Infographic

Top email and social media phishing subj... Infographic


2021 Thales Data Threat Report Infographic

APAC security budgets and priorities 202... Infographic
Global security insights 2021 Infographic
Is your fraud protection turning away cu... Infographic

Mobile Application Security report: Peri... Infographic


The CISO view on zero trust Infographic
Impact, costs and benefits of modern dat... Infographic
Big game hunting, ransomware dominate cy... Infographic
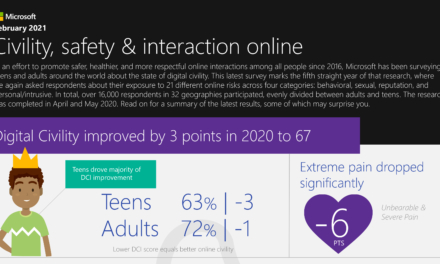
Civility, safety and interactions online Infographic

Top phishing email subjects Infographic


Looking back: 2020 cyberthreats Infographic

6 cybersecurity predictions for 2021 to ... Infographic

5 ways to combat fraud during the holida... Infographic

Growing need to secure cloud privileged ... Infographic

2020 Cost of a Data Breach Report Infographic

Authentication vs authorization Infographic
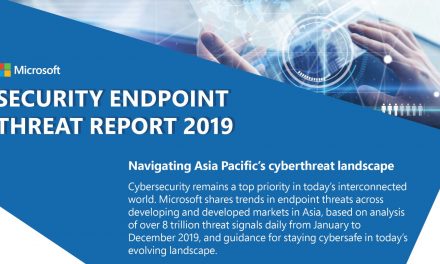
Asia Pacific Security Endpoint Threat Re... Infographic
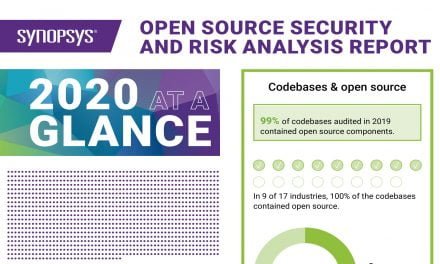
2020 open source security and risk analy... Infographic

Is it time to reinvent cybersecurity? Infographic
Prevalent malware exploiting COVID-19 Infographic
Backup and storage through the ages Infographic

Are APAC businesses ready for their tran... Infographic

5 predictions for digital payments in 20... Infographic

APAC organizations’ misplaced confidence... Infographic


Carbon Black Global Threat Report Infographic

2019 State of Enterprise Secure Access Infographic

A Look Back at the First Year of GDPR Infographic
Case Studies
Unlock Your Guide to Securing Business Critical Secrets
By Thales | Sep 24, 2024 | Case Study, Sponsored
Is your organization effectively managing access to sensitive secrets like credentials, API keys, and certificates across DevOps tools and cloud workloads? Secure Your Business Now – Download the e-Guide
Whitepapers
2024 Gartner® Magic Quadrant™ for SD-WAN
By Fortinet | Oct 15, 2024 | Sponsored, Whitepapers
Gartner® has positioned Fortinet highest for Ability to Execute for the fourth year in a row. And, for the fifth straight year, we’ve been named a Leader in the Magic Quadrant™ for SD-WAN.
-

Digital Acceleration Requires Converged Security and Networking
By Fortinet | Oct 3, 2024 | Sponsored, Whitepapers
-

5 Key IoT Capabilities to Look for in a Networking Solution
By Fortinet | Oct 3, 2024 | Sponsored, Whitepapers
-