Latest findings from the Google Threat Intelligence Group (GTIG) on North Korea remote workers find operations shifting sights from the US to Europe and APAC.
You must already have heard or read about IT workers from North Korea (DPRK) posing as legitimate remote workers to infiltrate companies and generate revenue for the regime.
Since GTIG’s last report analyzing the DPRK IT worker threat, crackdowns in the US have meant that these workers have found it increasingly challenging to seek and maintain employment in the country.
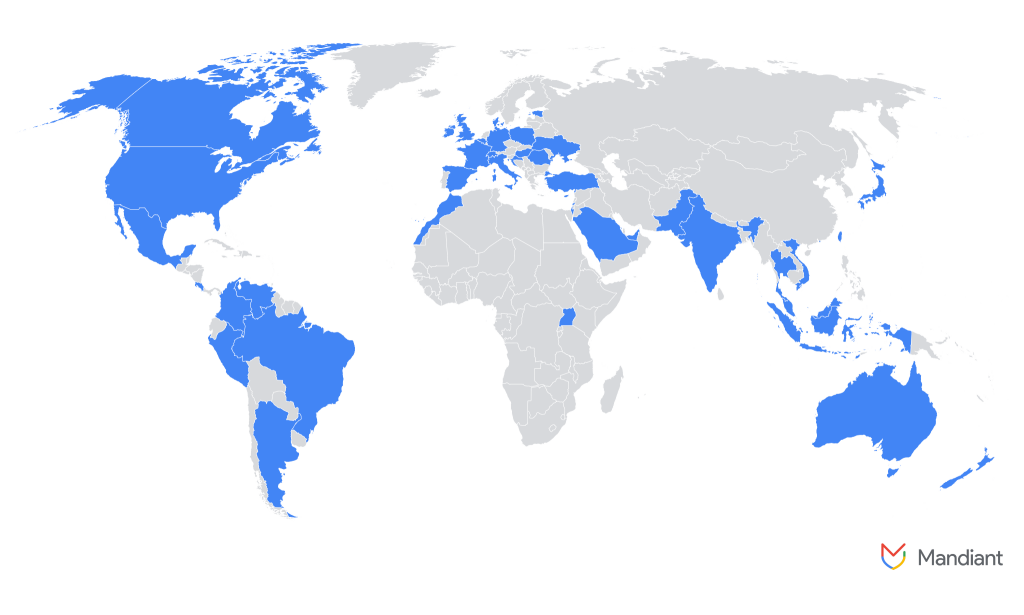
GTIG has identified an increase of active operations globally, particularly in Europe and APAC, over the past few months, suggesting that this threat is no longer limited to the US. The map below illustrates the countries impacted by DPRK IT workers:
GTIG’s findings include the following analyses:
- Targeting of defense industrial bases and European governments: In late 2024, GTIG identified a DPRK IT worker operating at least 12 personas across Europe and the US. This individual sought employment with multiple companies, particularly within defense industrial bases and European governments.
- Falsification of identities: DPRK IT workers’ tactics included fabricated references, rapport-building with recruiters, and using their own fake personas to vouch for credibility. In their efforts to secure these positions, they falsely claimed nationalities from a diverse set of countries, including Italy, Japan, Malaysia, Singapore, Ukraine, the United States, and Vietnam. The identities utilized were a combination of real and fabricated personas.
- New tactics include escalating extortion efforts: Since late October 2024, DPRK IT workers have significantly increased extortion attempts. Recently fired workers have threatened to leak proprietary data and source code to competitors. While these efforts initially targeted smaller organizations, law enforcement crackdowns have pushed them to go after larger enterprises with higher ransom demands.
Dr Jamie Collier, Lead Threat Intelligence Advisor, Europe, Google Threat Intelligence Group, commented: “A decade of diverse cyberattacks (encompassing SWIFT targeting, ransomware, cryptocurrency theft, and supply chain compromise), precedes North Korea’s latest surge. This relentless innovation demonstrates a longstanding commitment to fund the regime through cyber operations. Given DPRK IT workers’ operational success, North Korea will likely broaden its global reach. With APAC already impacted by these operations, this problem is set to escalate. These campaigns thrive on ignorance and will likely enjoy particular success in areas of APAC with less awareness of the threat.”
















