That is why organizations need to beef up basic mobile device management with real-time threat intelligence and frictionless all-round user protection.
From malicious apps and mobile ransomware to SMS phishing and OS exploits, the mobile threat landscape is a complex minefield for organizations to navigate, particularly with remote-employees’ home devices factored into the scenario.
In a data published in February 2022, 30% of workforces studied now worked exclusively from home. The same survey indicated that around 60% of respondents were actively facilitating hybrid working, giving their employees the freedom to choose where they log on. But how many of these organizations are fully prepared for the security demands of a truly mobile workforce?
According to Check Point Software Technologies researchers, the number of weekly cyberattacks on corporate networks in their customer base had peaked at an average of 900 attacks per organization in Q4 2021. Across the entire year, they recorded a 50% increase in weekly attacks from 2020.
Far from being a coincidence, these surges were more likely a reflection of cybercriminals taking advantage of the expanding mobile ecosystem running within organizations worldwide.
The emerging mobile threat
Mobile malware threats are not just designed to impact individuals; they are used to extort and steal data from corporate networks. Here are some notable threats to watch out for:
- NSO Group’s Pegasus, notorious for its ability to gain full control of iOS and Android devices via an elaborate zero-click exploit. Last year, it was widely reported that Pegasus had been used to target the mobile devices of more than 50,000 devices around the world, including those of high-level business executives.
- In its wake, a Macedonian-based group has created Predator spyware, designed to infect target devices via single-click links sent over WhatsApp. Both Pegasus and Predator are representative of a general shift toward social media and messaging apps as a way to steal credentials and infiltrate corporate networks.
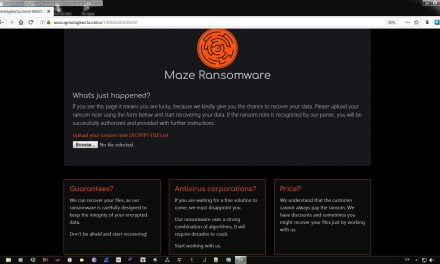
- In August 2021, an Android trojan known as FlyTrap was found to have compromised more than 10,000 Facebook accounts across more than a hundred countries. Not long after, a fraudulent version of WhatsApp designed to deliver the Triada banking trojan made its way onto the Android store, putting thousands of devices at risk. Toward the end of the 2021, a new malware known as MasterFred gained traction by using fake login overlays to steal credit card information from Twitter and Instagram users.
- SMS phishing, or ‘Smishing’ attempts have proven to be effective attack vectors. Check Point researchers have noted that the FluBot botnet still managed to return in the wild in 2021 despite having been dismantled by authorities earlier in the year. In 2021, UltimaSMS campaign launched a widespread SMS scam that leveraged more than 150 apps in the Google Play Store to sign victims up to a ‘premium’ SMS subscription service without their knowledge, stealing money and additional access privileges as a result.
- Finally, the banking malware landscape is rife with adaptive, difficult-to-detect malware families that extort business and harvest financial information. Trickbot, Qbot and Dridex are prominent malware that exhibit botnet-like features, used by ransomware campaigns to drop malware onto infected devices. Dridex was even among the first malware to be distributed via the ongoing Log4j vulnerability. In September 2021, malicious Android applications targeted the PIX payment system and its mobile banking apps. These applications abused Android’s Accessibility Services (AAS) in order to siphon money from PIX transactions while remaining largely undetected.
These emerging mobile threats are real, and are only the tip of the iceberg, according to Check Point.
Keep our guards up
How can organizations strike a balance between protection, customer data privacy and maintaining low friction in the user/customer experience? Are mobile device management (MDM) solutions enough to keep data safe?
The difficulty with mobile devices is that they are vulnerable to several attack vectors, including the application, network and OS layers. If an organization wants to guard against mobile malware proactively instead of reactively, it needs more than the basic level of monitoring afforded by most MDM solutions.
To be constantly on guard against zero-day phishing campaigns, adopt solutions that also use real-time threat intelligence and URL filtering to block access to known malicious websites from any browser. A holistic mobile device protection system also enforces conditional access, ensuring that if any device does become infected, it will be unable to access corporate applications and data. Furthermore, all that protection must also be designed to minimize disruptions to employees or customers.
As mobile ecosystems continue to expand, the attack surface area will expand right along with them. Therefore, mobile security is no longer an option or a token responsibility for organizations. Check out more tips for mobile device end users and bookmark CybersecAsia.net for regular updates and vendor-neutral thought leadership stories.