Suspected to be linked to Russia, a highly disruptive malware suite could be unleashed on Ukraine, NATO and critical industrial complexes.
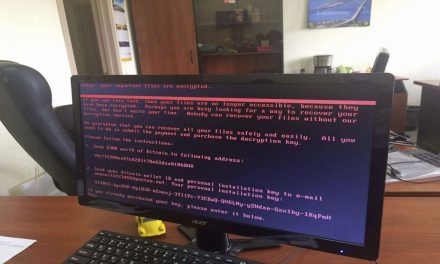
A new state-sponsored campaign based on a malware tools that attack critical infrastructure and industrial automation equipment has been discovered by cyber researchers.
Dubbed INCONTROLLER, the malware tools can interact with specific industrial equipment embedded in different types of machinery leveraged across multiple industries. The malware poses a critical risk to organizations leveraging the targeted equipment, and have been described by researchers to be “an exceptionally rare and dangerous cyberattack capability”.
INCONTROLLER includes three tools that enable attackers to send instructions to a variety of different industrial control system (ICS) devices embedded in different types of machinery across various critical industries. It is feasible that each tool could be used independently, or the actors may use the three tools to attack a single environment to:
- Shut down critical machinery
- Sabotage industrial processes
- Disable safety controllers to cause physical destruction of machinery that could potentially lead to the loss of human lives
- Target machine automation solutions whose use cases span from supporting simple, repetitive machines to complex modular machines in distributed architectures:
- OPC servers; Schneider Electric Modicon M251, Modicon M258, and Modicon M221 Nano PLCs;
- Other devices leveraging Modbus and Codesys may also be affected
- Omron NX1P2 and NJ501 PLCs and R88D-1SN10F-ECT servo drive
- Other devices from NJ and NX PLC series may also be affected
Remembering Triton/Stuxnet
Additionally, INCONTROLLER is “very likely state sponsored” and contains “capabilities related to disruption, sabotage, and potentially physical destruction,” being comparable to Triton and Stuxnet: The former was a cyber threat that in 2017 had been used to attempt to disable an industrial safety system to cause a power outage in Ukraine in 2016. The latter was another state-sponsored malware that sabotaged the Iranian nuclear program in 2010.
As a result, researchers believe “INCONTROLLER poses the greatest threat to Ukraine, NATO member states, and other states actively responding to Russia’s invasion of Ukraine.” According to Nathan Brubaker, Director, Intelligence Analysis, Mandiant, the firm disclosing its investigations on INCONTROLLER: “While we are unable to definitively attribute the malware, we note that the activity is consistent with Russia’s historical interest in ICS. Organizations should take immediate action to determine if the targeted ICS devices are present in their environments and begin applying vendor-specific countermeasures, discovery methods, and hunting tools.”
Mandiant is also tracking two additional malware tools that may be related to this threat activity that are affecting Windows-based systems.
- One of the tools exploits CVE-2020-15368 in the AsrDrv103.sys driver, which would result in installation and exploitation of a vulnerable driver. ASRock motherboards may be leveraged in some human-machine interfaces (HMIs) and engineering workstations in OT environments.
- The other tool, ICECORE, is a backdoor providing reconnaissance and command and control functionality.
It is possible that these tools could be used to support the overall attack lifecycle in an INCONTROLLER attack by exploiting Windows-based systems in IT or operational technology (OT) environments.