Are organizations training Finance personnel and all staff to be vigilant?
A cybersecurity firm’s analysts have noticed that, in recent weeks, several organizations have reported attempts by attackers to deceive finance departments into processing fraudulent payments.
Attackers had sent emails that appeared to come from company executives, such as the CEO, instructing staff to pay invoices for supposed consulting services. The emails typically imitated ongoing correspondence between the firm’s leadership and external contractors or law firms.
In some cases, the attackers had referenced previous messages or included fabricated email threads to make the requests appear legitimate. Also, while the sender’s display name matched that of a known executive or partner, the actual email address was unrelated and changed frequently.
Some of these Business Email Compromise (BEC) incidents included fake invoices as attachments, while others had relied solely on the content of the email to prompt urgent action. The primary tactic was to exploit employees’ trust in internal communications, and their reluctance to question requests from senior management.
Other incidents had featured emails that mimicked communications between a CEO and contractor firms to request urgent payment for a fake invoice, but the invoices were not attached, according to a spokesperson for Kaspersky, the firm that disclosed this incidence-response trend.
Organizations need to train staff to be vigilant for BEC attacks:
- Making sure emails involving sensitive and important requests from key leaders have the correct originating email address and domain, and matching sender name.
- When a sender is legitimate, but the content of the message seems strange, staff should contact the supposed sender via an alternative, unhackable means of communication.
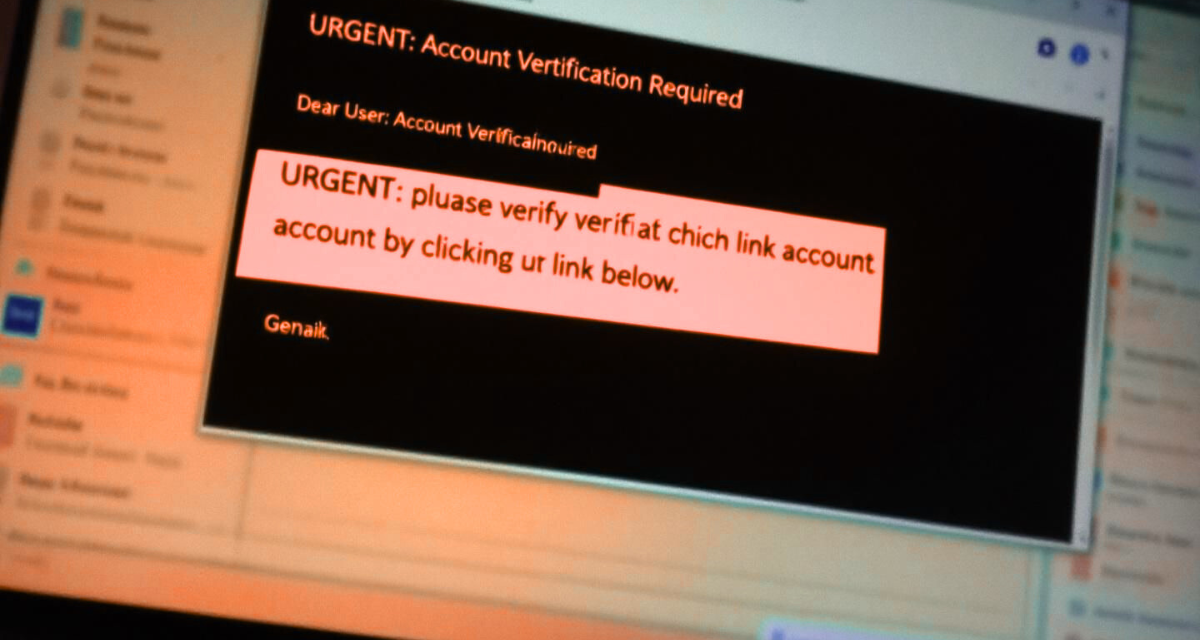
- Being constantly on guard for phishing attempts and spoofed URLs, such as a “1” instead of “I”, or “0” replacing the letter “O”.
- Using the proper email authentication protocols, email security filters and AI/ML features to flag suspicious communications and behavioral patterns.
Finally, even though cybercriminals and malicious insiders may learn a target firm’s processes and system weaknesses, they will find it difficult to pull off a BEC successfully when the organization’s policies mandate non-negotiable multi-stage, multi-party identity verifications for financial transactions or sensitive data.