Dangling fake job offers and rigged coding tests to lure applicants, a state-sponsored threat group has been looting billions in cryptocurrencies.
Threat researchers have found that North Korean state-sponsored hackers have been waging a sophisticated campaign against cryptocurrency developers, exploiting professional networking and coding platforms to deliver custom malware that can evade traditional detection tools.
The threat group is believed to have stolen over US$1bn from the cryptocurrency sector in 2023 alone, including a US$1.5bn heist from a Dubai-based exchange, and a US$308m theft from a Japanese firm.
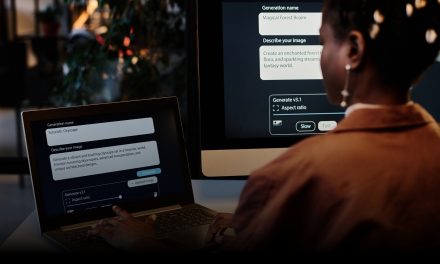
Attackers have posed as recruiters on professional career networking platforms, targeting developers with enticing job offers. After initiating contact, the malicious actors send a PDF with a job description, followed by a coding challenge hosted on GitHub. These repositories appear legitimate but have been secretly modified to include malicious code, typically in Python or JavaScript, tailored to each victim’s expertise.
Method of attack
Once a developer runs the code, two custom malware strains — RN Loader and RN Stealer — are deployed.
- RN Loader collects system information and executes further malicious payloads
- RN Stealer is designed to harvest sensitive data such as SSH keys, cloud credentials and even iCloud Keychain data on macOS systems.
The malware uses advanced evasion techniques such as YAML deserialization and Embedded JavaScript templating to run in memory, minimizing its footprint and making detection difficult.
A key feature of this campaign is its selectivity: the malicious payloads are only delivered after the attackers verify the victim’s IP address, geolocation, and system configuration, ensuring that only high-value targets are compromised. The attackers are also mimicking legitimate infrastructure, using Command-and-Control servers that resemble normal web traffic to avoid raising suspicion.
The campaign has prompted platforms such as LinkedIn and GitHub to remove accounts and repositories linked to the threat group.
Security experts from Palo Alto’s Unit 42, the teams uncovering and monitoring the North Korean threat group, advise developers to be wary of unsolicited job offers and coding challenges, to separate personal and work devices, and to carefully vet any external code before execution.