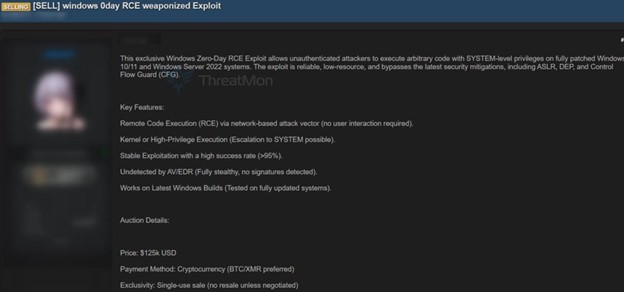
The premium exploit supposedly grants SYSTEM privileges remotely, bypasses protections, evades detection, and requires no user action!
On 20 August 2025, an high criticality advanced Windows Zero Day remote code execution (RCE) exploit targeting fully patched Windows 10, Windows 11, and Windows Server 2022 systems was advertised for sale, according to security researchers.
A rogue seller has advertise the weaponized exploit code as capable of granting attackers SYSTEM-level privileges without requiring prior authentication or any user interaction, posing a critical risk to both enterprise and individual users.
This zero-day can supposedly:
- bypass core Windows security protections including Address Space Layout Randomization (ASLR), Data Execution Prevention (DEP), and Control Flow Guard (CFG), making traditional defenses ineffective
- leverages a network-based vector that requires no user action, significantly broadening the potential for compromise
- satisfy the requirements of advanced persistent threat groups and ransomware syndicates
- evade detection by antivirus and endpoint detection and response (EDR) solutions, boasting of a stealthy profile with a success rate reportedly above 95%
- confer elevated privileges that allow attackers to gain direct kernel-level control of vulnerable systems, effectively escalating from standard user privileges to SYSTEM, the highest level of Windows permissions. This capability enables extensive manipulation and control over affected machines, facilitating persistent and damaging attacks
With an asking price of US$125,000 and exclusive sale conditions, the exploit’s premium status underscores the growing market for sophisticated cyberattack tools, according to the source of the news about the Dark Web advertisement, ThreatMon. Buyers are prohibited from reselling the exploit unless that privilege has been explicitly paid for.
This unfolding zero-day highlights the urgent need for organizations to monitor anomalous kernel-level activity, ensure timely patching of systems, and utilize advanced threat intelligence to detect and mitigate zero-day exploitation attempts. Security professionals and system administrators are being advised to stay abreast of emerging threat intelligence, apply mitigations as they become available, and report suspicious activities related to zero-day exploits to the appropriate authorities and vendors.