Timely updates can cut SE Asia organizations’ data breach damage costs and penalties, according to a global study.
While vulnerabilities are inevitable in any software, regular patching and updates can minimize the risk of hacker exploitation. That is the main reason why organizations are constantly being advised to install software fixes as soon as they are available, even if the updates can sometimes be difficult or a time-consuming.
In South-east Asia, according to one cybersecurity firm, 54% of organizations may need to update more regularly. Kaspersky’s own 31-country global survey of 5,266 decision makers showed that in this region, 38% of SMEs (small- and medium- sized enterprises) and 48% of larger enterprises in June 2020 were still working with unpatched operating systems. As for outdated software, their figures showed an incidence of 33% for SMEs and 43% for the rest.
According to the firm’s General Manager (Southeast Asia), Yeo Siang Tiong: “It may seem costly for companies to renew their software or opt for their legal versions especially at this time of an unprecedented crisis. It is, however, an investment which can save you money in the long run. In fact, our research showed that enterprises using obsolete or unpatched systems will pay US$437,000 more in case of a data breach—a 126% increase compared with the projected cost of US$354,000 for those companies without outdated (critical resources).”
Reasons for the update lag
Yeo asserted that SMEs in SE Asia can also save 9% of attack costs if they use updated and legal software, with US$94,000 being the toll of a single data breach.
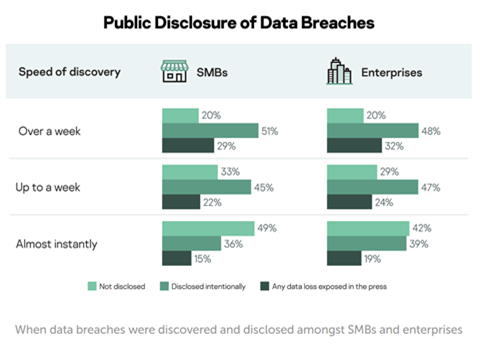
Besides the additional cost in case of a data breach, 49% of both SMEs and enterprises from the region also admitted to experiencing cyberattacks because of unpatched vulnerabilities in the software applications and devices they used. This was 9% more than the global average of 40%.
According to the study, the top reasons why SEA organizations kept using such tools were:
- Some line employees refused to work with new software and devices, so exceptions for them were made (57%)
- In-house apps could not run on new devices or operating systems (52%)
- C-level staff were excluded from software update regimes (45%)
- Not enough resources to update everything at once (17%)
The reasons cited are insufficient to hold up to scrutiny in a court of law. Organizations should observe best practices and maintain strong cyber hygiene for updating of critical operation systems and other critical software, on top of a strong endpoint protection solution.