Amid growing supply chain vulnerabilities and a thriving underground economy, APAC is experiencing a notable rise in state-sponsored cyber-attacks.
Ensign InfoSecurity recently released its sixth Cyber Threat Landscape Report (CTLR) 2025, revealing a significant rise in state-sponsored cyber-attacks across Asia-Pacific (APAC) in 2024. Meanwhile, an increasingly sophisticated underground economy and growing supply chain vulnerabilities are driving the scale and success of attacks across the region.
This report is based on insights drawn from Ensign’s proprietary telemetry and intelligence gathered across the APAC region in 2024. It provides a comprehensive view of the evolving threat landscape Some key findings include:
1. Rising state-sponsored attacks across APAC
State-sponsored threat groups across APAC are on the rise, accounting for a notable number of cyberattacks in 2024. These groups are usually well-resourced and have high-level capabilities. Their modus operandi is characterized by stealth, persistence, and strategic patience, positioning themselves for future operations.
2. Thriving underground economy powers persistent threats
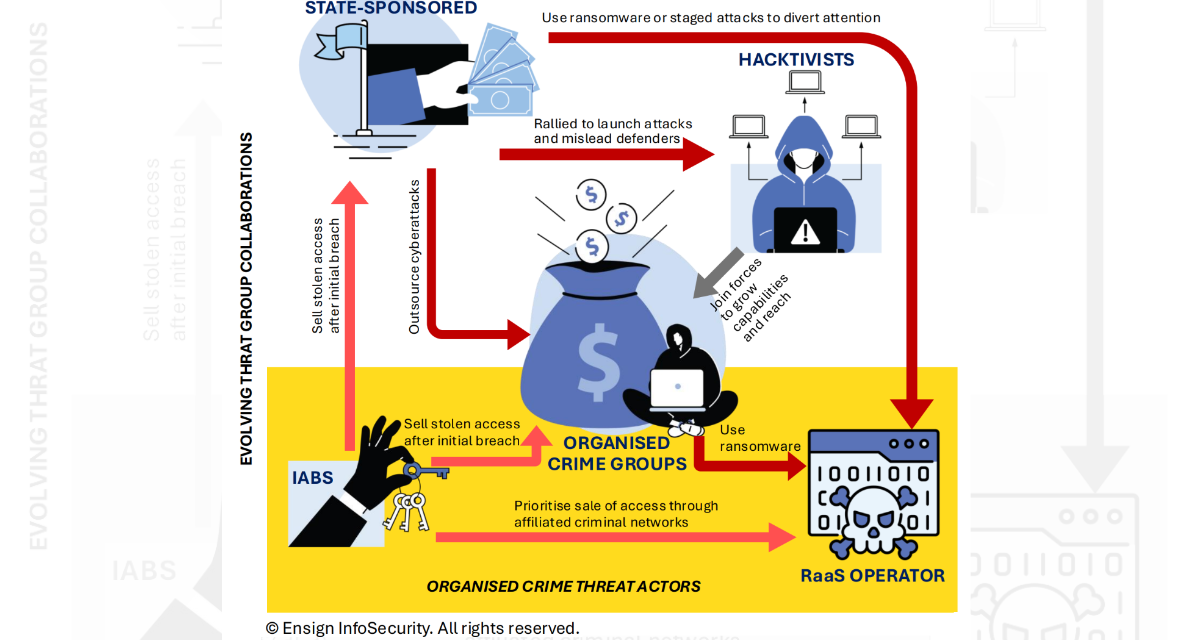
The cyber underground has evolved into a mature and highly collaborative economy. Threat actors including ransomware groups, Initial Access Brokers (IABs), and hacktivists work in tandem; each specializes in a piece of an attack while pursuing multiple income streams. IABs, for instance, have adopted a “breach once, sell to many” model, monetizing initial access by selling it to multiple parties. In the meantime, state-sponsored groups were observed to sub-contract attack tasks to other threat actors, adding layers of complexity to cyber campaigns. Such multi-stakeholder participation in cyberattack campaigns makes it increasingly difficult to attribute attacks to the original masterminds.
“Threat actors are no longer operating in silos. The cyber underground today functions as an illicit, dynamic, and highly collaborative marketplace,” said Xiang Zheng Teo, Vice President of Advisory, Ensign InfoSecurity. “These alliances, combined with widening supply chain vulnerabilities, have made threat groups more capable, persistent, and difficult to dislodge.”
3. Cyber supply chain under sustained attack
The report reveals increasing sophistication in supply chain compromises, where hardware, software, and service providers are targeted for stealthy access into organizations. The Business and Professional Services (BPS) firms, such as legal, accounting, and consulting, have become prime targets. Because of the trusted relationships these firms maintain with their clients, they often possess large amounts of sensitive client data. Yet, they typically lack deep defensive capabilities, making them attractive pathways for attackers seeking broader network penetration.
4. Dwell time quadrupled, indicating growing detection gaps
Notably, compared to 2023, incident-response dwell time (the duration attackers remain undetected within networks) has risen significantly across industries. Across APAC, the maximum dwell quadrupled from 49 to 201 days, while the minimum dwell more than doubled to 7 days. This signals that cyber criminals had a much wider window to steal data, move across networks, and cause damage.
“We are increasingly seeing many organizations being compromised without them even realizing it. As digitization deepens, AI technologies become more pervasive and threat actors grow increasingly sophisticated, organizations must move beyond assumptions of safety,” Teo added. “It is clear that the cyber space is not benign. Organizations must continue to validate their defenses, fix the weak links, and ensure that their cyber posture is operating at a level of readiness that meets today’s threat landscape.”