Attackers exploited an open-source extension vulnerability to install malware, harvest sensitive credentials, and exfiltrate high-value cryptocurrency before takedown.
A fake software extension for the Cursor AI development environment, which leverages technologies from Visual Studio Code, has resulted in a Russian blockchain developer losing US$500,000 in cryptocurrency after unwittingly installing and using it.
The compromised extension, falsely presented as “Solidity Language” in the Open VSX marketplace, was promoted to the top of search results through artificial inflation of its download count to 54,000 to boost interest.
The incident, which first occurred in June 2025, is only now coming to light after the completion of several investigative stages. Cybersecurity experts required extensive time for forensic analysis to fully uncover the attack method:
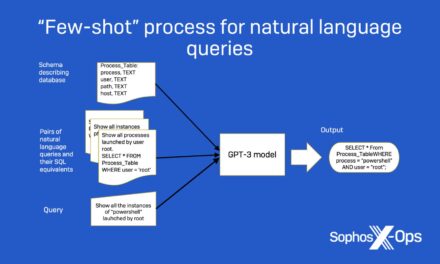
- Upon installation, the extension added no genuine functionality but instead ran a PowerShell script that deployed ScreenConnect, granting attackers remote access to the victim’s system.
- This access enabled attackers to install additional malware, including the Quasar backdoor and PureLogs infostealer, which harvested sensitive data such as browser credentials and wallet seed phrases, facilitating the theft of digital assets.
- Investigation and reporting were delayed due to the need for:
- Comprehensive malware analysis and attribution
- Ongoing remediation efforts as the attackers republished the malicious package, eventually inflating its download count to nearly two million
- Victim confidentiality concerns and asset-tracing attempts with law enforcement
- Coordinated takedown and industry alerts to prevent further infections and inform the broader developer community.
This case exposes persistent risks within open-source developer tool marketplaces, particularly where ranking algorithms and moderation practices can be abused. It highlights how attackers leverage trust in popular AI and coding environments to target crypto-focused developers with sophisticated social engineering and technical exploits.
According to a spokesperson for Kaspersky, the firm that disclosed the incident: “Spotting compromised open-source packages with the naked eye is becoming increasingly difficult. Threat actors are using increasingly creative tactics to deceive potential victims, even developers who have a strong understanding of cybersecurity risks — particularly those working in the blockchain development field.”