Many of the older stolen credentials are still active because victims may not even know about infostealer malware risks.
In one of the largest credential leaks ever discovered, a massive data breach has lost over 183m email passwords to cybercriminals, including millions linked to Gmail accounts.
This 3.5-terabyte dataset, containing 23bn records, was the result of nearly a year of infostealer malware activity that steals usernames, passwords, and URLs from infected devices.
On 21 October 2025, the news was broken by Troy Hunt, operator of the breach notification platform Have I Been Pwned. The Australian security researcher has confirmed that about 16.4m of the total number of stolen data were never seen in prior breaches, signaling a large number of new compromises.
Additionally, the cybersecurity firm that monitored and aggregated the data, Synthient, had found the stolen credentials circulating on underground marketplaces and Telegram channels where hackers trade large batches of compromised information.
Despite the scale of the breach, Google has stated there was no direct breach of Gmail servers: instead, the credentials had been obtained from malware infections on users’ devices or phishing attacks. The firm has refuted reports of a unique breach of their free email service, and has urged users to enable two-step verification, adopt passkeys, and promptly change compromised passwords.
Cyber hygiene still lagging worldwide
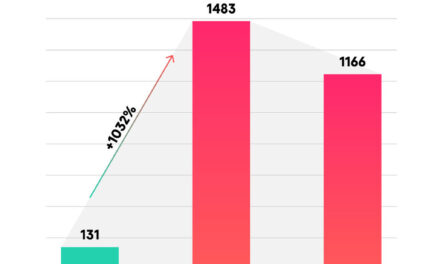
The growing threat of infostealer malware poses severe risks, as these programs have increased stolen credentials by 800% in early 2025, according to one threat intelligence index. The stolen data enables large-scale credential stuffing attacks, which exploit password reuse across multiple online accounts and services, including banking and cloud storage.
Internet users and Gmail account owners can check their exposure on HaveIBeenPwned.com. Experts recommend strong, unique passwords, activation of multi-factor authentication, reluctance to click suspicious links, and use of password managers to mitigate risks.
This breach disclosure underscores the critical need for cautious cybersecurity practices to protect digital identities from malware-driven theft and its wider consequences across the internet.