Malicious releases expose SSH keys, cloud credentials, and Kubernetes secrets in developer environments through a hidden WAV‑based payload.
A threat group’s supply-chain campaign has moved from security tools to a widely-used communications software development kit, with malicious Telnyx Python package releases on PyPI used to steal credentials from developer environments.
According to Telnyx, unauthorized versions 4.87.1 and 4.87.2 were published at 03:51 UTC on 27 March and removed by 10:13 UTC the same day, and that the firm’s platform itself was not compromised.
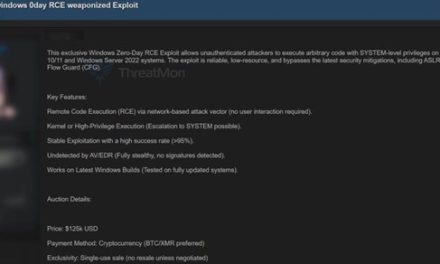
Researchers note the attack is part of a broader campaign that previously hit projects including Trivy, Checkmarx KICS, and LiteLLM. Endor Labs has linked the Telnyx incident to the same threat actor (TeamPCP) by pointing to shared infrastructure and techniques, including a reused RSA key from the earlier LiteLLM compromise.
The Telnyx package matters because it is the official Python SDK for the firm’s communications platform, and is used in applications that handle voice, messaging, and API authentication. That makes it an attractive target: compromised installations can expose SSH keys, cloud credentials, Kubernetes secrets, and database passwords stored in developer or build environments.
In this case, what stood out was the malware delivery method:
- Security researchers said the payload was hidden inside a legitimate WAV audio file downloaded at runtime, then decoded and executed in memory, which reduces the chance of detection by static scanning.
- Socket said the malicious code ran at import time, bypassing common checks that focus on install-time hooks.
- The compromise appears to have been enabled by stolen publishing credentials rather than a GitHub repository breach, according to researchers and the package maintainers’ notice.
- Security advisories note that anyone who installed or upgraded Telnyx during the affected window should treat their systems as compromised, and proceed to rotate credentials, and review network and cloud logs for suspicious activity.
The incident shows how a single poisoned package can become a launch point for cloud compromise, especially when the software sits close to secrets, API keys, and infrastructure access.