The LockBit group may have been busted, but its co...
By CybersecAsia editors | Apr 30, 2024
Were cyberattackers evading detection less efficie...
By CybersecAsia editors | Apr 26, 2024
How medical devices manufacturer Tuttnauer protect...
By CybersecAsia editors | Apr 23, 2024
Understanding the “multiplier effect” of digital fraud in the region
By CybersecAsia editors | May 2, 2024
One survey in APAC has had respondents in two industries pointing to losses that were much more than what was defrauded
Read MoreCyber resilience requires leaders that manage risk with full organizational support: report
By CybersecAsia editors | May 2, 2024
Organizational and leadership mindset gaps in supporting CIOs could weaken or undermine even seemingly comprehensive response plans, as one survey suggests
Read MoreSophisticated China-linked DNS threat actor exposed
By CybersecAsia editors | May 2, 2024
The threat group’s use of advanced distraction and obfuscation techniques could be a precursor of future, larger-scale global DNS attacks
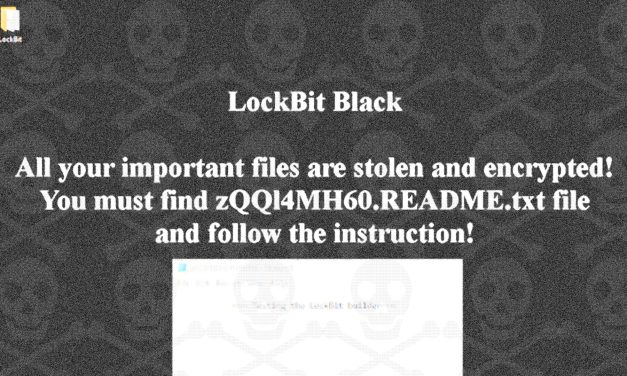
Read MoreThe LockBit group may have been busted, but its code lives on
By CybersecAsia editors | Apr 30, 2024
Its malware builder, leaked in 2022, is now being used to create dangerous variants of self-propagating ransomware
Read MoreWere cyberattackers evading detection less efficiently in 2023?
By CybersecAsia editors | Apr 26, 2024
According to one cybersecurity firm’s incident metrics, the mean dwell time was the lowest ever recorded by its teams globally
Read MoreHow medical devices manufacturer Tuttnauer protects patient and personal-data safety
By CybersecAsia editors | Apr 23, 2024
In running a cloud-based portal to link its smart medical equipment, the firm has also implemented third-party end-to-end cybersecurity vigilance
Read MoreHow much of automated internet traffic contains malicious activity?
By CybersecAsia editors | Apr 22, 2024
One cybersecurity firm’s 20234 global bot activity data can shed some light on this area of growing concern
Read MoreLarge language models have their strengths and weaknesses: analysis
By CybersecAsia editors | Apr 22, 2024
In a balanced testing process, one widespread LLM has been evaluated for vulnerabilities and strengths, to demonstrate no room for complacency
Read MoreMore RATs discovered in official Android app store
By CybersecAsia editors | Apr 19, 2024
Cybercriminals have been modifying open source remote access trojans (RATs) for embedding into seemingly legitimate apps to infiltrate “trusted” app stores
Read MoreWhen GenAI chatbots start pretending to be stupid to gain human trust…
By CybersecAsia editors | Apr 19, 2024
This may be a signal that the limited human intellect, in trying to play God, may be underestimating Pandora’s box
Read More
- 1
- ...
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- ...
- 116
Voters-draw/RCA-Sponsors
CybersecAsia Voting Placement
Gamification listing or Participate Now
|
PARTICIPATE NOW |
|
|
Vote Now -Placement(Google Ads)
Top-Sidebar-banner
Whitepapers

Securing Industry 4.0
The world is advancing to Industry 4.0 in full swing, and this is a key …Download Whitepaper
Secure Access Service Edge (SASE) Solutions for Today’s Work-From-Anywhere (WFA) Environment
Organizations are turning to Secure Access Service Edge (SASE) solutions for securing remote work environments, …Download Whitepaper
Identity Has Breached the Ecosystem
This whitepaper explores the dual nature of identity in cybersecurity, emphasizing its role in both …Download Whitepaper
Fortanix Buyers Guide for Modern Key Management and Data Security
This document underscores the pressing challenges in key management and data securityDownload Whitepaper
Middle-sidebar-banner
Case Studies

How medical devices manufacturer Tuttnauer protects patient and personal-data safety
In running a cloud-based portal to link its smart medical equipment, the firm has also …Read more
AI vulnerability testing: Knowing the In’s and Out’s of proper red teaming
To test the safety/security of a generative AI feature, what unchartered bugs and human testing …Read more
Real estate logistics provider GLP steps up to zero trust architecture
With its physical and digital footprint growing, the global firm’s outdated legacy security stack has …Read more
Identity security woes now a thing of the past for Heng Leong Hang
The retail chain was grappling with numerous cyber risks in its IT infrastructure until it …Read more