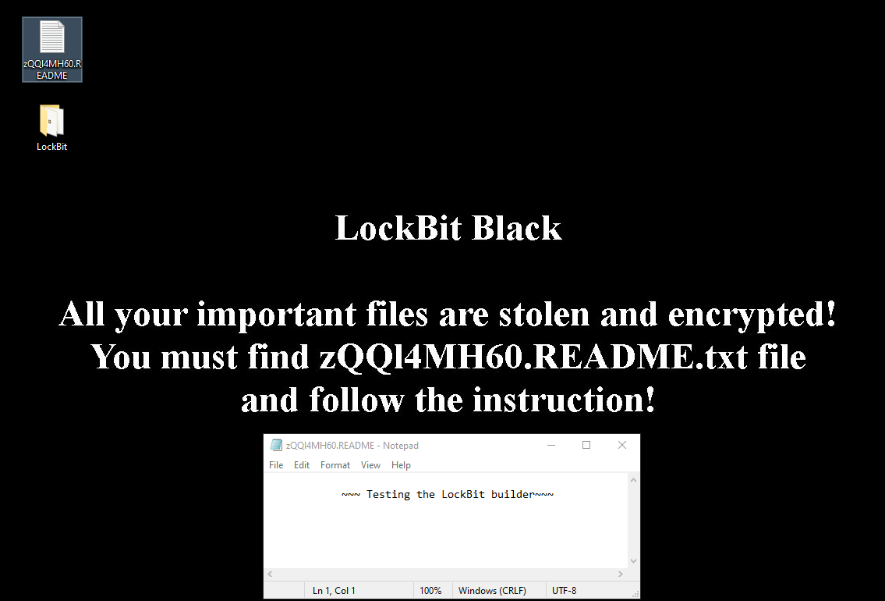
Its malware builder, leaked in 2022, is now being used to create dangerous variants of self-propagating ransomware
In February 2024, an international law-enforcement operation seized control of the LockBit ransomware-as-a-Service group. A week later, the group was supposedly back in action.
Now, a recent incident in Guinea-Bissau has revealed that adversaries have crafted their own variant of LockBit-3.0-based encryption malware equipped with self-propagation properties that can create an uncontrolled avalanche effect. This is due to infected hosts attempting to spread the malware further within the victim’s network.
According to analysts from Kaspersky, the resurgence of LockBit ransomware in a variant form has the following features:
- Impersonation: Leveraging illicitly-acquired credentials, the threat actor impersonates the system administrator with privileged rights to gain access to the most critical areas of the corporate infrastructure.
- Self-propagation The customized ransomware can spread autonomously across the network using highly-privileged domain credentials and conduct malicious activities, such as disabling Windows Defender, encrypting network shares, and erasing Windows Event Logs to encrypt data and conceal its actions.
- Adaptation: Along with the aforementioned features, the malware uses customized configuration files to tailor itself to the specific victimized company’s architecture. For example, the attacker can configure the ransomware to infect only specific files, such as all .xlsx and .docx files, or only a set of specific systems. The attackers use the SessionGopher script to locate and extract saved passwords for remote connections in the affected systems.
Incidents involving various types of techniques based on the leaked LockBit 3.0 builder, but lacking the self-propagation and impersonation capabilities found in Guinea-Bissau, have been occurring regularly in various industries and regions tracked by Kaspersky —Russia, Chile, and Italy; and the geographical scope of attacks may be further expanding.
According to the firm’s Incident Response Specialist, Cristian Souza: “The LockBit 3.0 builder was leaked in 2022, but attackers still actively use it to create customized versions — and it doesn’t even require advanced programming skills. This flexibility gives adversaries many opportunities to enhance the effectiveness of their attacks. It makes these kinds of attacks even more dangerous, considering the escalating frequency of corporate credential leaks.”