Actually, it is all up to cyber defenders. Here is one AI-based cyber strategy that turns risk into responsiveness.
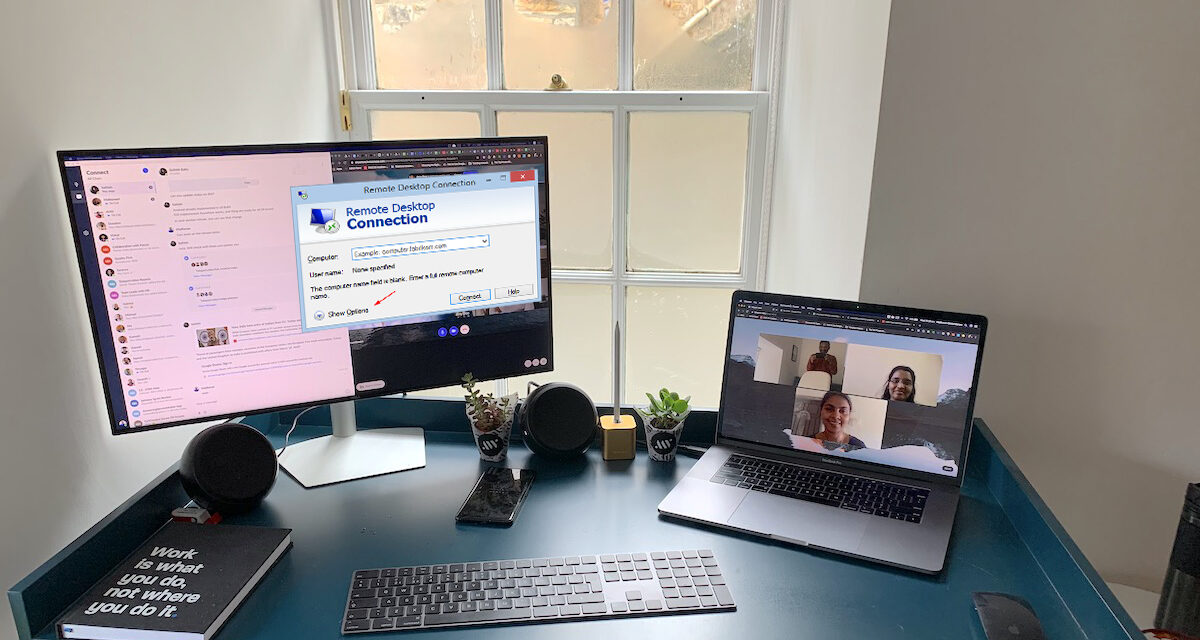
With the rise of remote-working worldwide, there are now almost five million Remote Desktop Protocol (RDP) servers exposed to the Internet: around two million more than before the pandemic.
Events such as the Florida water plant incident, where an attacker attempted to manipulate the chemical concentration in the water supply of a whole city, show how fatal the consequences of such a cyber threat can be.
Just last month, cybersecurity firm Darktrace detected a server-side attack at a technology company in the Asia-Pacific region (APAC). The hackers brute-forced an RDP server and attempted to spread throughout the organization. If the attempt were not detected in time, the attackers could have created a botnet and used it to cause serious damage, potentially launching a ransomware or distributed denial-of-service (DDoS) attack.
All it takes to lose control
According to Max Heinemeyer, Director of Threat Hunting, Darktrace, all it takes is one vulnerable RDP server for a threat actor to gain an initial foothold into an organization and spread laterally to build their botnet army. A bot is simply an infected device that can be controlled by a malicious third party. Once a network of these externally-controlled bots has been accumulated, a hacker can perform a range of actions, including:
- Exfiltration of user credentials and payment data.
- Uploading Trojan malware to the server, which opens a backdoor to the system while masquerading as legitimate software.
- Deploying ransomware, as seen last year in a Dharma attack.
- Renting out access to the company’s infrastructure to other threat actors.
- Mining cryptocurrency with the CPUs of zombie devices.
In fact, there is little that attackers cannot do once they have gained remote access to these devices. Botnet malware tends to contain self-updating functions that allow the owner to add or remove functionality. And because the attackers are using legitimate administrative RDP credentials, it is extremely difficult for traditional security tools to detect this malicious activity until it is far too late.
Rise of Cybercrime-as-a-Service
There are now subscription-based and rental models of cybercriminal service on the Dark Web, such as Ransomware-as-a-Service and botnets-for-hire, for as little as US$20 per hour. In fact, some of these kits are even legal, and market themselves as ‘IP stressers’ or ‘booters’, which can be used legitimately to test the resilience of a website, but are often exploited and used to take down sites and networks.
These developments have sparked a new wave of DDoS and botnet malware attacks as hackers capitalize on the added financial incentive to create botnets and rent them out.
‘Botnet builder’ tools help low-skilled attackers create bots by providing botnet malware and assisting with the initial infection. Sophisticated RDP attacks have blossomed as a result of these kits, which lower the skill-threshold of such attacks and thus make them widely accessible.
Botnet malware and automation
With hackers using automation and turnkey Cybercrime-as-a-Service solutions, Internet-facing RDP servers remain one of the most common initial infection vectors.
The ease of compromise has actually shot up since the rise of RDP as the solution for remote working. It is only matter of time before exposed servers are exploited. Furthermore, heavily automated attacks are constantly running and can spread rapidly across the organization. In such cases, it is vital for security teams to be made aware of malicious activity on devices as quickly as possible.
As a proponent of AI-driven cybersecurity, Heinemeyer believes that organizations can benefit from self-learning cybersecurity watchdog. It continuously scans for anomalous activity in users and devices across the digital environment and can shut down threats at machine speed.
Moreover, the increased network visibility greatly reduces the attack surface and identifies badly maintained shadow IT, thereby providing an extra layer of security over the digital business.