Why pay thousands when you can get Premium crypto-trading service for a full year at no cost?
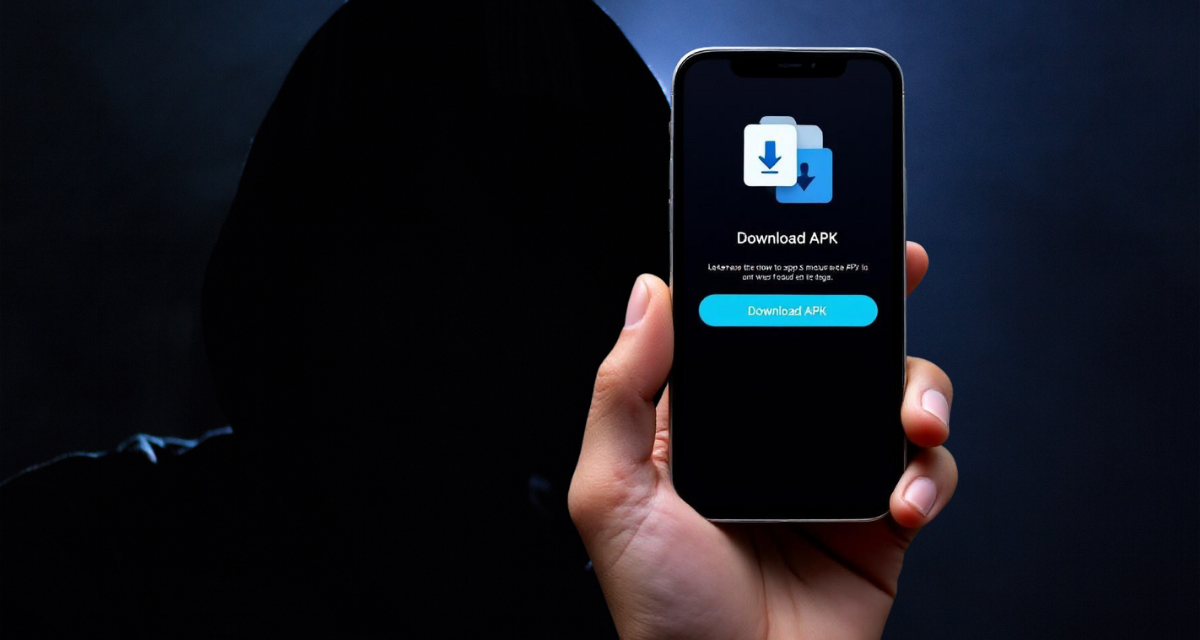
A new wave of malicious advertising targeting Android users has been uncovered, spreading advanced crypto-stealing malware disguised as legitimate mobile apps.
The campaign currently employs fake ads on Meta’s platforms, offering a purported free premium version of a popular trading app for Android that costs thousands of dollars per year to use.
The ads mimic familiar branding and visuals to deceive users into clicking and downloading a malicious .apk file from fraudulent websites that closely imitate official app pages. A commonly used prompt in the ads is: “Why pay a year when you can get Premium for a full year at no cost?”
Instead of the legitimate software, users end up downloading a sophisticated trojan designed to steal cryptocurrency credentials and other sensitive information. Once installed, the malware requests extensive device permissions, including accessibility access, often hidden behind fake update prompts. This access allows the malware to perform numerous intrusive actions such as overlaying screens with deceptive messages, stealing lock screen PINs, and extracting data from installed apps, including financial and authentication apps. Other details of the malware include:
- Indications that it is a significantly evolved version of the Brokewell trojan, functioning as both spyware and a remote access tool.
- If a desktop user clicks on the ad, random and benign content will be delivered instead.
- It communicates with its command servers through encrypted channels, enabling attackers to remotely control infected devices, capture screenshots, record audio, dump clipboard contents, scrape email inboxes, and harvest two-factor authentication credentials.
- Its capabilities likely make it one of the most advanced Android threats linked to malvertising campaigns observed so far.
To boost distribution, the attackers localize their fake ads in multiple languages and impersonate numerous well-known brands and financial platforms. Although initially targeting Windows desktop users, this operation now actively pursues users of the Android operating system.
Since 22 July 2025 the global campaign, uncovered by Bitdefender, has used at least 75 malicious ads. By 22 August 2025, tens of thousands of users in the EU alone had been affected by the trojan malware.