If you click on it, you’re through…
Lemon_Duck is one of the more advanced types of cryptojacker payloads that threat researchers have seen.
The malware creators continuously update the code with new threat vectors and obfuscation techniques to evade detection, and the miner itself is ‘fileless’, meaning it remains memory resident and leaves no trace of itself on the victim’s file system.
Researchers from SophosLabs have tracked the frequency with which Lemon_Duck uses specific attack vectors, and signs indicate that this wiley malware launches test attacks to determine the best way to proceed at full scale.
One of many COVID-19 opportunistic malwares
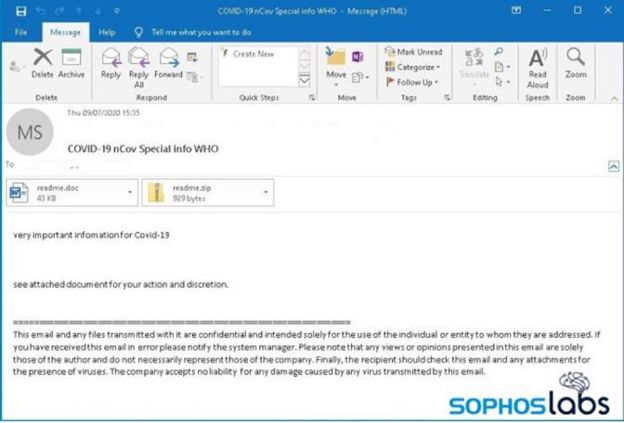
The cryptojacker feeds on public interest in COVID-19 ‘special news’ as well as major event information such as the end-of-year holiday sales, tax-filing deadlines or other current events. In a series of coronavirus-themed emails in a mass spam campaign, recipients receive malicious attachments that start the sneaky ball rolling.
Once victims’ compromised machines are in control, Lemon Duck malware makes them unwitting super spreaders by sending the same emails to all their Outlook contacts. Said Rajesh Nataraj, Senior Threat Researcher, Sophos: “It’s hard to overstate the risk of harm here, since people are more likely to trust messages from people they know than from random internet accounts.”
Lemon Duck malware does this all on the fly with code that generates the email messages and attachments dynamically, pulling from a list of subject lines, message body text, and other content that include phrases like “The Truth of COVID-19,” “COVID-19 nCov Special info WHO,” or “HALTH ADVISORY: CORONA VIRUS” (sic).
“The typo HALTH instead of HEALTH in the subject line or body copy is a clue that this is email is malicious and no-one should click on it. Similar to Advanced Persistent Threat (APT) groups, Lemon_Duck attackers use different threat vectors to explore and test which vector will work best. With security detections getting better, these trial-and-error attacks help them figure out what works, or doesn’t, and give them better a chance of succeeding,” Nataraj said.