A hornet’s nest of new evasion techniques make it one of the hardest malwares to detect and analyze to date.
FinFisher, also known as FinSpy or Wingbird, has been in circulation as a surveillance tool capable of gathering various credentials, file listings and deleted files, as well as various documents, livestreaming or recording data, and gaining access to a webcam and microphone.
Its Windows implants have been detected and researched several times up to 2018 when FinFisher appeared to have gone under the radar.
Now, researchers from Kaspersky have revealed that the Wingbird spyware has undergone recent updates in its Windows, Mac OS, Linux code, and in software installers. It now features four-layer obfuscation and advanced anti-analysis measures employed by the spyware’s developers, as well as the employment of a UEFI rootkit to infect victims’ computers.
Even software installers for legitimate software such as TeamViewer, VLC Media Player and WinRAR were in some cases infected with malicious code that could not be connected to any known malware. That is, until one day researchers discovered a website in Burmese that contained the infected installers and samples of Wingbird for Android, helping to confirm that all the software had been trojanized with the same spyware.
The findings suggest a high emphasis on defensive evasion, making Wingbird one of the hardest-to-detect spyware to date.
Four ways of evading detection
Previous versions of the spyware infected applications with trojan code exposed to view. However, new samples of the infection show that the trojan code is now protected by two components: a ‘non-persistent Pre-validator’ and a ‘Post-Validator’.
The first component runs multiple security checks to ensure that the device it is infecting does not belong to a security researcher. Only when the checks pass, is the Post-Validator component provided by the server—this component ensures that the infected victim is the intended one. Only then would the server start deployment of the full-fledged trojan platform.
Four complex custom-made obfuscators slow down attempts to analyze the spyware. On top of that, the trojan also employs peculiar ways to gather information. For instance, it uses the developers’ mode in browsers to intercept traffic protected with a HTTPS protocol.
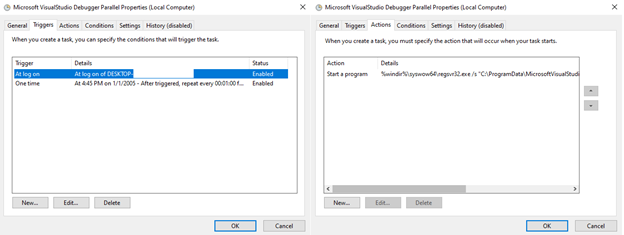
Finally, a sample of FinFisher has been found to replace the Windows UEFI bootloader (a critical software component that launches the operating system) with a malicious one. This way of infection allows attackers to install a rootkit without the need to bypass boot-time security checks.
UEFI infections are very rare and hard to execute, but the FinFisher method stands out due to their evasiveness and persistence. In this case the attackers did not infect the UEFI firmware itself but the next boot stage: the malicious module was installed on a separate partition and could control the boot process of the infected machine.
According to Igor Kuznetsov, Principal Security Researcher, Kaspersky Global Research and Analysis Team (GReAT) the amount of work put into making FinFisher not accessible to security researchers is worrying and somewhat impressive. “It seems like the developers put at least as much work into obfuscation and anti-analysis measures as in the trojan itself. As a result, its capabilities to evade any detection and analysis make this spyware particularly hard to track and detect. The fact that this spyware is deployed with high precision and is practically impossible to analyze also means that its victims are especially vulnerable, and researchers face a special challenge: having to invest an overwhelming amount of resources into untangling each and every sample.”
Kuznetsov believes complex threats such as FinFisher demonstrate the importance for security researchers to cooperate and exchange knowledge as well as invest in new types of security solutions that can combat such threats.













