They are deploying fake crypto ads, using stealthy malware, and spoof crypto-celebrities to lure victims with promises of quick riches.
According to the threat researchers from a cybersecurity firm, a persistent malvertising campaign is plaguing Facebook, leveraging the reputations of well-known cryptocurrency exchanges to lure victims into a maze of malware.
The threat involves the deployment of cleverly disguised front-end scripts and custom payloads on users’ devices, all under the guise of legitimate cryptocurrency platforms and influencers.
The malvertising campaign has been operating for several months, consistently producing new advertisements. It heavily leverages the imagery and trust associated with cryptocurrency brands, and it remains active with fresh ads appearing regularly.
Tactics used
The initial malware is allegedly delivered via covert communication between a malicious website’s front end and local host, a method that evades detection by most security vendors. By orchestrating malware deployment through a seemingly harmless intermediary, attackers remain stealthy. Next:
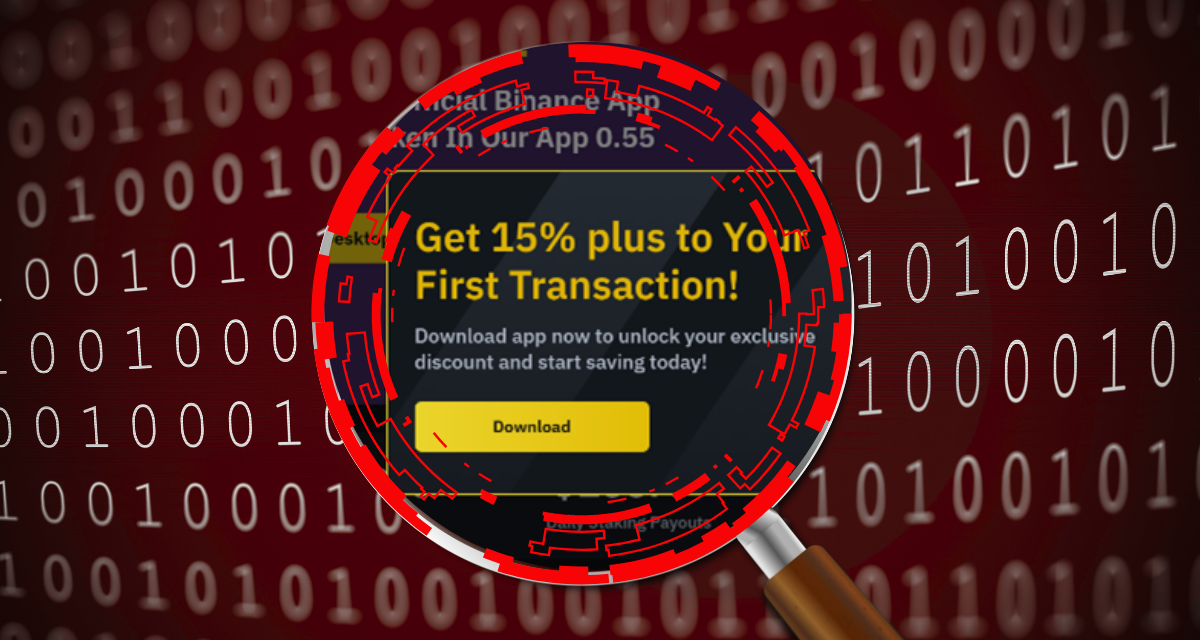
- Hundreds of ads impersonating trusted cryptocurrency exchanges and trading platforms have been put online, to drastically increase the odds that potential victims will view the malicious ads and be convinced to interact with the prompts. The cybercriminals use Meta’s ad network to tout quick financial gains and crypto bonuses, with some ads seeking to bolster credibility by featuring the image of public figures such as Elon Musk or Cristiano Ronaldo.
- Advanced tracking and evasion: The threat actors use sophisticated anti-sandbox checks, only delivering malware to users who meet specific demographic or behavioral profiles. Query parameters related to Facebook Ads are used to detect legitimate victims, while suspicious or automated analysis environments receive benign content. Any user who views a malicious ad is redirected to a website that impersonates a known cryptocurrency platform, with subsequent prompts to download a “desktop client”. However, if the site detects suspicious conditions (for example, missing ad-tracking parameters or an environment typical of automated security analysis), it displays harmless, unrelated content instead. Also, no malicious content will be displayed for users who loaded the website without the specific query parameters of the Facebook ads: some examples being utm_campaign, utm_content, fbid, cid. If the user is not logged into Facebook, or if the IP address and operating system do not interest the attackers, the website will not display malicious content.
- Newer variants take a step further, prompting users to open the site using Microsoft Edge; opening it with other browsers leads to random, non-malicious content, further complicating detection efforts. One particularly deceptive instance is a Facebook clone that mirrors TradingView’s official Facebook page. From the profile pictures to posts and comments touting a free ‘Annual Ultimate Subscription’, everything is fabricated, except for the central buttons that redirect victims to the real Facebook website.
- Researchers have uncovered hundreds of Facebook accounts promoting these malware-delivering pages, all pushing financial benefits. In one notable example, a single page ran over 100 ads in a single day (9 April, 2025). While many ads are quickly removed, some garner thousands of views before takedown. Targeting is frequently fine-tuned, such as focusing on men aged 18+ in Bulgaria and Slovakia — to maximize reach.
- All analyzed malware samples had the name installer.msi and measured around 800KB. After installation, the malicious software would open the page of the impersonated entity through msedge_proxy.exe. Victims also receive a suspicious DLL file that launches a local .NET-based server on ports 30308 or 30303 (in a newer version). By dynamically adjusting to the victim’s environment and continuously updating payloads, the threat actors maintain a resilient, highly evasive operation. Multiple layers of obfuscation, sandbox checks, and real-time payload evolution make this campaign a sophisticated challenge for researchers and security providers.
The threat researchers, hailing from Bitdefender Labs, have citing facing and uncovering multiple techniques that had prevented end-to-end analysis of the threat — from the measures taken on the malicious websites (displaying non-malicious content based on traffic metadata), to anti-sandbox actions (for example, the looped PowerShell task would not download the final payload in dynamic analysis environments).
Despite the sophistication and innovation of the campaign, immunization involves compliance with the golden rules of basic cybersecurity hygiene.

A typically alluring fake ad luring people to download sophisticated multi-stage malware