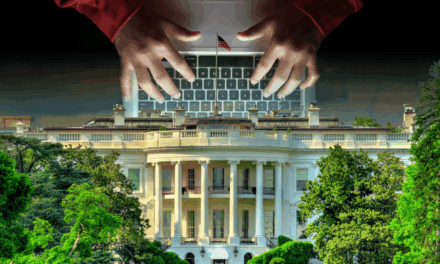
Going by one cybersecurity firm’s Q1 numbers, ransomware groups have been using disinformation to complicate efforts to assess true attack volumes.
In releasing a summary of Q1 2025 cyber incident data, a cybersecurity firm has pointed out some cybersecurity trends.
First, Q1 saw its user ecosystem encountering a 126% year-on-year surge in ransomware activity among a specific set of business users, with 74 ransomware groups publicly naming 2,289 victims on data leak sites. Even excluding a mass disclosure of 300 victims linked to one ransomware group’s exploitation of a file transfer platform vulnerability, the monthly average of reported victims has remained historically high at over 650, compared to roughly 450 per month throughout the firm’s 2024 data. Including this group, the average has risen to 760 victims per month, a new high for ransomware activity within the firm’s user base.
Second, the most active ransomware group in the firm’s Q1 data had focused on encryption-less attacks, relying on data theft and extortion rather than file encryption. This group had exploited zero-day vulnerabilities in widely-used third-party file transfer products, primarily affecting North American organizations: 83% of victims were based in the United States and Canada. The consumer goods and services sector accounted for 33% of this group’s victims, reflecting the customer profile of the targeted platform, which is popular among firms in manufacturing, supply chain, and logistics.
Third, other notable ransomware actors in the firm’s Q1 metrics included:
- a group that rapidly grew following the disruption of a major ransomware operation in early 2024, naming 228 victims by aggressively recruiting affiliates with favorable profit-sharing.
- another group that had claimed 167 victims but was found to recycle or fabricate victim reports, a tactic increasingly common among ransomware actors to inflate reputations and intimidate targets.
- a newer group that had emerged using AI-assisted malware development, lowering technical barriers for attackers and blurring lines between hacktivism and financially motivated crime.
Fourth, the geographic distribution of victims in the user base has largely reflected established patterns, with Western developed nations most frequently targeted, although some groups showed distinct regional focuses.
According to Sergey Shykevich, Threat Intelligence Group Manager, Check Point Software, the firm sharing its Q1 incident data analysis: “The 126% spike in ransomware (incidents) is more than just a number, it’s a signal. This denotes smarter, faster, and harder-to-track campaigns and groups that try to manipulate our mind. AI tools, fake victim claims, and regionally tailored tactics mean organizations must move beyond reactive defenses and adopt prevention-first, intelligence-led security.”