Between 2018 and 2020, credential stuffing and SQL injection attacks made them much richer than their victims, according to a study.
What kind of criminal activity targeted the retail, travel, and hospitality sectors between July 2018 and June 2020? What are some examples of criminal ads from the Dark Net illustrating how cybercrooks can cash in on successful attacks and stolen data?
These questions prompted intelligent edge platform provider Akamai to release a security report to address: “Loyalty for Sale – Retail and Hospitality Fraud” this week.
Between July 2018 and June 2020, Akamai had observed more than 100 billion credential stuffing attacks in total. In the commerce category (comprising the retail, travel, and hospitality industries), 63,828,642,449 incidents were recorded. More than 90% of the attacks in the commerce category had targeted the retail industry.
During the COVID-19 pandemic-related lockdowns in Q1 2020, criminals took advantage of the global panic and circulated password
combination lists targeting each of the commerce industries featured in the report. It was during this time that criminals started recirculating old credential lists in an effort to identify new vulnerable accounts, leading to a significant uptick in criminal inventory and sales related to loyalty programs.
Credential stuffing is recyclable
According to Steve Ragan, Akamai’s security researcher and author of report: “Criminals are not picky— anything that can be accessed can be used in some way. This is why credential stuffing has become so popular over the past few years. These days, retail and loyalty profiles contain a smorgasbord of personal information, and in some cases financial information, too. All of this data can be collected, sold, and traded or even compiled for extensive profiles that can later be used for crimes such as identity theft.”
Credential stuffing is not the only way that criminals target the retail, travel, and hospitality industries. They target organizations in these industries at the source using SQL Injection (SQLi) and Local File Inclusion (LFI) attacks.
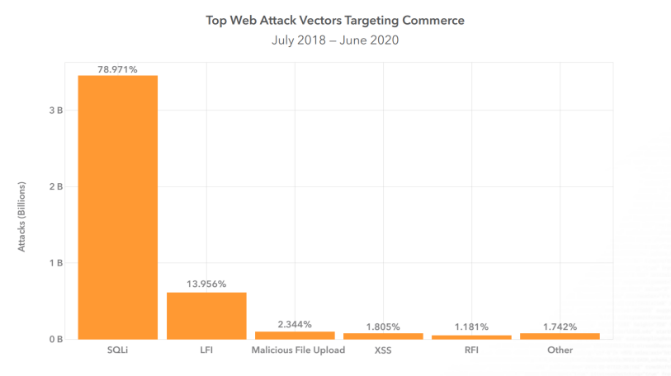
Between July 2018 and June 2020, Akamai observed 4,375,711,860 web attacks against retail, travel, and hospitality, accounting for 41% of the overall attack volume across all industries. Within this data set, 83% of those web attacks targeted the retail sector alone. SQLi attacks were an evident favorite among criminals, accounting for just under 79% of the total web application attacks against retail, travel, and hospitality.
Shopping season hacker frenzy
As the global economy prepares for the holiday shopping season, it does so in an environment that has changed radically due to the pandemic, the report asserted. Consumers will not be standing outside of bricks-and-mortar stores waiting for the latest deals in the same way they have in the past. They are going to log-in, collect their reward points, and maybe use loyalty programs to gain some discounts or other perks just for being a member.
Considering everything that goes into a successful loyalty program, as well as the information people need to provide in order to take part—cybercrooks have everything they need to get started in a number of crime-related ventures, from account takeovers, to straight-up identity theft. So, while an individual’s loyalty to a merchant, airline, or hotel chain may not literally be for sale, there is a good chance the account associated with such programs might be, the report said.
“All businesses need to adapt to external events, whether it’s a pandemic, a competitor, or an active and intelligent attacker,” Ragan concluded. “Some of the top loyalty programs targeted required nothing more than a mobile number and a numeric password, while others relied on easily-obtained information as a means of authentication. There is an urgent need for better identity controls and countermeasures to prevent attacks against APIs and server resources.”













