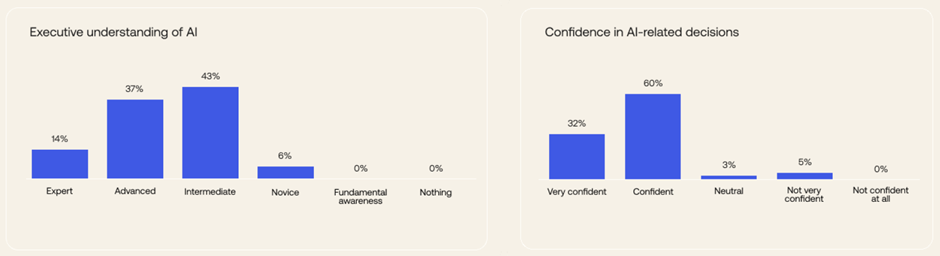
BG: While C-suite leaders’ outlook on AI may be strong, their understanding of the technology is less so. About 43% described their grasp of AI as intermediate, while another 37% claimed to have a more advanced handle on the technology. Only 14% assessed themselves as AI experts, the highest option.
While there is room to learn more about AI, most respondents expressed confidence in their ability to make AI-related decisions: 92% said they were either confident or very confident. CTOs lead the way, with 51% describing themselves as very confident in their AI decisions.
Execs have a similarly rosy outlook on how well their employees grasp the threats that AI poses. More than two-thirds (67%) said their workforces are either very informed or somewhat informed about such threats.
Given that AI is not a new concept, it isn’t surprising that leaders express high confidence. However, generative AI introduces a new tech stack. In the past, the AI data stack has been more in the backend running its processes. With generative AI-powered product launches, data is moving into organizations’ customer-facing production stack, so it’s imperative to make AI security and privacy posture a high priority.
What does AI adoption look like for organizations in APAC compared to other regions?
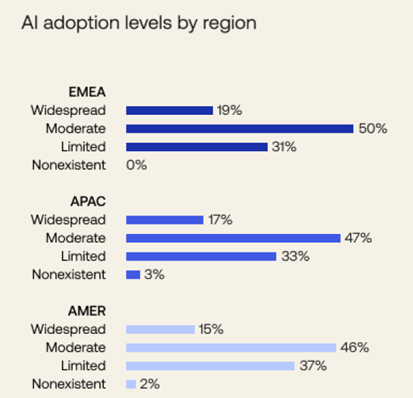
BG: Okta’s AI at Work report revealed that executives in EMEA report slightly more widespread (19%) and moderate (50%) levels of AI adoption when compared with APAC and AMER. Most executives who see their organizations having moderate to widespread adoption of AI are from the technology industry, followed by finance and banking and professional services.
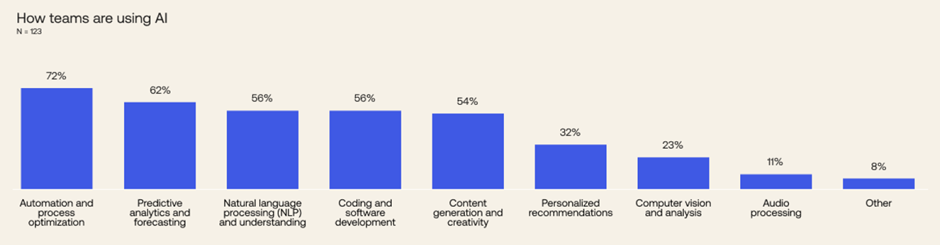
Across the business, AI is being used to some degree for security purposes at 71% of surveyed executives’ companies, with more than half (59%) of executives characterizing the use as moderate, with specific projects or initiatives. In APAC and EMEA, the top AI use cases at the workforce level are automation and process optimization. In AMER, it’s natural language processing (NLP) and understanding.
Looking ahead: What do APAC organizations need to do to increase their AI maturity and security posture?
BG: The best defense against AI is AI. As bad actors ramp up their efforts, it’s the legitimate businesses that have embraced AI that stand the best chance of defending against these attacks. Organizations should look at integrating the latest AI/ML-powered threat protection tools that offer autonomous, real-time response within their identity and security stack, and continually review their cyber-defense strategies to level up with an evolving threat landscape.
As AI adoption increases globally, Identity is key to helping businesses embrace the technology’s undeniable power without sacrificing security. It’s the entry point to an organization’s data and infrastructure, and hackers know it.
This is why we have a long-term plan to lead the industry in the fight against identity attacks. We call this the Okta Secure Identity Commitment. We’ve made strong progress, rolling out safeguards like stronger phishing-resistant tools for employees and newly available products and enhancements on both our Workforce and Customer Identity Clouds.

















