Agentic AI: The next great productivity hack or th...
By Victor Ng | Mar 18, 2026 | Features, Newsletter | 0
Building trust in Asia’s financial sector with dig...
By Victor Ng | Mar 16, 2026 | Features, Newsletter | 0
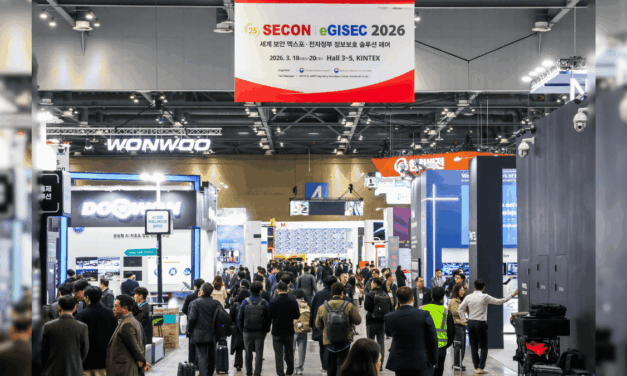
Physical and digital security converge in APAC
By Edward Lim | Apr 6, 2026 | Features
AI-driven biometrics and surveillance are redefining protection across Asia Pacific.
Read MoreAgentic AI: The next great productivity hack or the ultimate security nightmare of 2026?
By Victor Ng | Mar 18, 2026 | Features, Newsletter
As we navigate the technological landscape of 2026, a new category of software – agentic AI – is rapidly reshaping how individuals and organizations work.
Read MoreMisconfigured AI: Hype or real threat to APAC Infrastructure?
A press release sparks alarm: but cyber experts emphasize governance gaps, operational flaws over misconfiguration hype in regional grids and ports
Read MoreBuilding trust in Asia’s financial sector with digital identity innovations
By Victor Ng | Mar 16, 2026 | Features, Newsletter
As fintech innovation accelerates across Asia, digital identity has become the foundation of trust between financial institutions and their customers.
Read MoreIoT trends APAC enterprises cannot ignore in 2026
With new connectivity standards and rising regulatory complexity across the region, the IoT landscape is shifting.
Read MoreBeyond firewalls – addressing cybersecurity blind spots
Is your organization focusing on the exposures that matter most, or is your cybersecurity investments misallocated?
Read MoreWhere are financial fraud and AML regulations heading in S E Asia?
As Southeast Asia’s digital economy scales, scams and AI-enabled social engineering are scaling with it, widening the attack surface for banks, fintechs, and digital platforms.
Read MoreHow AI is reshaping dating in Asia
By CybersecAsia editors | Feb 9, 2026 | Features, Newsletter
Romance is in the air as Valentine’s Day approaches. But while dating platforms accelerate AI adoption to better meet user needs and demands, a recent survey recommends caution…
Read MoreEmerging third-party cyber risks via agentic AI
As organizations accelerated AI adoption in 2025, a new and underappreciated category of third-party risk has emerged: agentic AI.
Read MoreRethinking customer identity for financial cybersecurity
What should banks in Asia Pacific pay attention to this year to protect themselves and their customers?
Read More
Voters-draw/RCA-Sponsors
CybersecAsia Voting Placement
Gamification listing or Participate Now
|
PARTICIPATE NOW |
|
|
Vote Now -Placement(Google Ads)
Top-Sidebar-banner
Whitepapers

Closing the Gap in Email Security:How To Stop The 7 Most SinisterAI-Powered Phishing Threats
Insider threats continue to be a major cybersecurity risk in 2024. Explore more insights on …Download Whitepaper
2024 Insider Threat Report: Trends, Challenges, and Solutions
Insider threats continue to be a major cybersecurity risk in 2024. Explore more insights on …Download Whitepaper
AI-Powered Cyber Ops: Redefining Cloud Security for 2025
The future of cybersecurity is a perfect storm: AI-driven attacks, cloud expansion, and the convergence …Download Whitepaper
Data Management in the Age of Cloud and AI
In today’s Asia Pacific business environment, organizations are leaning on hybrid multi-cloud infrastructures and advanced …Download Whitepaper
Middle-sidebar-banner
Case Studies

Cyber protection for medical clinics in Singapore
As Singapore’s healthcare sector becomes increasingly digital and interconnected, clinics are facing heightened cyber risks, …Read more
India’s WazirX strengthens governance and digital asset security
Revamping its custody infrastructure using multi‑party computation tools has improved operational resilience and institutional‑grade safeguardsRead more
Bangladesh LGED modernizes communication while addressing data security concerns
To meet emerging data localization/privacy regulations, the government engineering agency deploys a secure, unified digital …Read more
What AI worries keep members of the Association of Certified Fraud Examiners sleepless?
This case study examines how many anti-fraud professionals reported feeling underprepared to counter rising AI-driven …Read more
Bottom sidebar
Other News
PQShield Advances Japan’s Quantum-Safe Security Transition Through CRYPTREC ML-KEM Evaluation
Japan can now begin deploying …Read More »Cambridge Global Advisors Awarded Grant to Build Cyber Capacity Among Women in the Pacific from Australia’s Department of Foreign Affairs and Trade
WASHINGTON, April 2, 2026 /PRNewswire/ …Read More »NEC Appoints New Managing Director to Drive Next Phase of Growth in Malaysia
KUALA LUMPUR, Malaysia, April 1, …Read More »Dragos Appoints Kaori Nieda as Country Manager to Drive Expansion in Japan
HANOVER, Md., April 1, 2026 …Read More »Kingsoft Cloud Announces Unaudited Fourth Quarter and Fiscal Year 2025 Financial Results
BEIJING, March 25, 2026 /PRNewswire/ …Read More »