Even more dire consequences could surface if password reuse habits by compromised users are exploited by hackers.
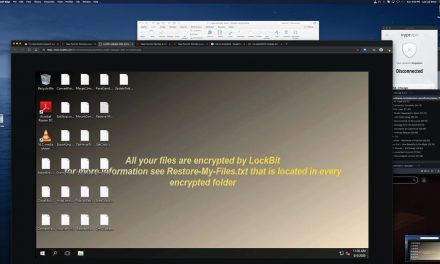
A list containing plaintext usernames and passwords, along with IP addresses for over 900 VPN servers belonging to Pulse Secure VPN, has been published online as well as shared on a hacker forum used by cybercriminals.
As Pulse Secure VPN servers are usually employed as access gateways into corporate networks to enable remote staff to connect to their office apps, this leak is of particular concern. When compromised, these types of devices can allow hackers to gain easy access to a company’s entire internal network.
According to Doron Naim, Cyber Research Group Manager, CyberArk Labs: “While VPNs provide employees and third parties with remote access, they also provide a direct data tunnel to corporate networks (that) can be used to provide privileged access to critical business systems and applications, that is, the targets that are most valuable for hackers. In this case, usernames, plain-text passwords, and IP addresses were exposed. In and of itself, that’s concerning, but attackers could also take advantage of password reuse habits to conduct credential-based attacks on internal systems and business applications like HR and payroll—providing a backdoor to critical data and assets.”
In light of this and other well-publicized breaches, it is important for organizations to examine other ways to provide remote access to the most sensitive parts of the corporate network, said Naim.
This includes Zero Trust access, granular access to only the critical system instead of the whole network; biometric multi-factor authentication, and just-in-time provisioning, in combination with session isolation and management.
“This would allow VPNs to be dispensed-with completely in some instances, including for privileged access to critical systems. Additionally, it reinforces the need to patch, whether the software lives in the cloud or the enterprise itself,” said Naim.
Update: Response from Pulse Secure
Since the publication of this disclosure on CybersecAsia.net, Pulse Secure’s chief marketing officer, Scott Gordon, has issued a security advisory SA44101 for CVE-2019-11510 and declared that the company has been proactively contacting all customers to apply the patch fix. Gordon estimated that over 97% of customers have applied the patch and are no longer vulnerable.
His official response at this time is: “Pulse Secure takes vulnerabilities seriously and continues to apply industry best practices to expedite work with threat researchers and protect our customers. We urge all our customers deploy the security patch fix, available since April 2019, to protect themselves from threat actors and potential attacks. We have already contacted customers that have yet to apply the patch fix multiple times using contact information available to us, and we will continue to do so until they deploy the patch to all their systems.”