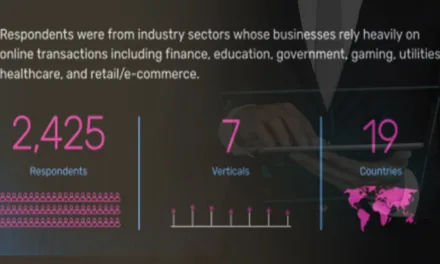
Data from a small international survey highlights respondents’ views on identity-security maturity, AI use, and deployment success in security practices.
Based on a June 2025 survey of 375 decision-makers in information technology, cybersecurity, and risk across parts of the Americas, Europe, and Asia* on identity security, an identity and access management solutions firm that commissioned it has shared some findings on maturity levels and capabilities were shared with the media.
First, 63% of the 375 respondents had indicated that their organizations were in the lowest or second-lowest level of maturity on a five-point scale of identity security management.
Second, respondents from organizations that ranked their own organization higher in identity security maturity had also indication higher adoption of AI-enabled detection capabilities such as identity threat detection and response and privileged account monitoring compared to those with lower identity maturity.
Other findings
Third, respondents from organizations that performed identity data cleanup before migration selected choices indicating 1.6 times higher likelihood of complete success in identity and access management tool deployment. Also:
- Respondents from organizations in level 3 or higher levels of identity security maturity selected choices indicating 4.5 times higher adoption of cloud data governance capabilities such as unified policy enforcement and real-time data access monitoring
- 30% of 229 respondents had selected identity and access management as the domain with highest perceived return on investment, compared to 5% for network security, 8% for application security, 10% for cloud security posture management, 12% for governance risk and compliance, 13% for data security, and 22% for endpoint detection and response
- 4% of respondents indicated their belief that their organizations regressed in identity security maturity in 2025
- Respondents from organizations in the middle- to higher- levels of identity security selected choices indicating 4 to 8 times higher adoption of real-time identity data synchronization, entity resolution, and automated lifecycle workflows compared to those ranking their organizations lower in the scale
- 25% of respondents had selected choices indicating their organizations positioned identity and access management as a strategic business enabler, while 57% had selected choices indicating it as a security control or compliance requirement
According to Matt Mills, President, SailPoint, the firm that commissioned the survey: “… Advances in AI, data management, and threat detection” were noted in relation to identity security, alongside mentions of unified visibility, expanded governance, and automated resilience.
*with more than half representing organizations with over 10,000 employees, and the majority from finance, technology, and healthcare sectors. Some responses were from a subset of 229 respondents. Details on data validation, potential respondent bias, or the appendix referenced for demographics are undisclosed, limiting full assessment of methodological rigor.