Cybercriminals are employing novel ways such as invisible spaces and confusing URLs to foil email scanning software and wary users.
Phishing emails and social media posts often contain harmful links that direct victims to fake websites where they could be tricked into downloading malware or reveal personal information such as login IDs and passwords.
As security systems become better at spotting these malicious links, cybercriminals are developing crafty new ways to hide them and slip past defenses unnoticed.
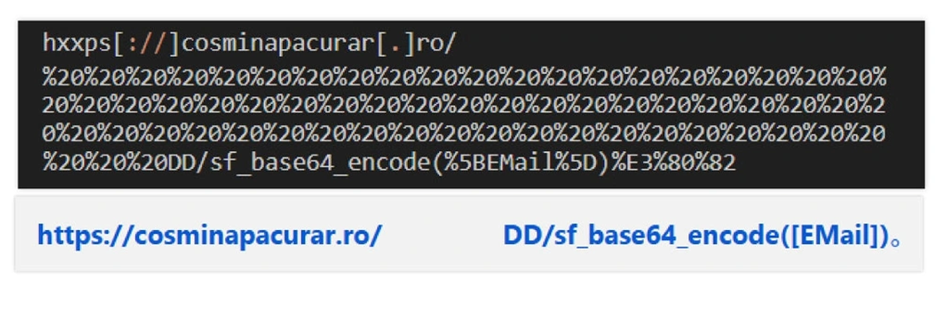
On 9 September 2025, one cybersecurity firm has shared some new findings about several clever tricks being used to obscure actual URLs. The methods are: Inserting invisible spaces (code %20) and unusual characters into web addresses, to push the malicious part of the link out of sight of security scanners or suspicious eyes. Attackers can also add fake elements such as a hidden email address or secret codes at the end of the links that can track victims or redirect them to malicious sites. To make their trap look more convincing, the attackers sometimes include fake verification tests such as CAPTCHA prompts that make the site appear legitimate.
- Inserting invisible spaces (code %20) and unusual characters into web addresses, to push the malicious part of the link out of sight of security scanners or suspicious eyes. Attackers can also add fake elements such as a hidden email address or secret codes at the end of the links that can track victims or redirect them to malicious sites. To make their trap look more convincing, the attackers sometimes include fake verification tests such as CAPTCHA prompts that make the site appear legitimate.
E.g.: A malicious URL padded with invisible spaces to be visually broken up into two parts that look harmless.
- Using the Redundant Protocol Prefix technique to craft a URL that is only partially hyperlinked or that contains invalid elements (such as two ‘https’ or no ‘//’) to hide the real destination of the link while ensuring the active part looks benign and legitimate and does not arouse suspicion.
This approach can also involve crafting links with multiple protocol prefixes or embedding trusted-looking names before the “@” symbol in URLs. This tricks users and security filters into believing the link is safe, while the real malicious site is hidden after the “@.”
Attackers can also use strange symbols such as backslashes or dollar signs (which are not normally used in URLs) to confuse scanning software.
E.g.: The link https:office365Scaffidips[.]azgcvhzauig[.]es\If04 looks harmless, but actually sends the browser to a malicious page azgcvhzauig.es - Creating fake domain names that look like official company subdomains, which further fools people into trusting the site. When users copy and paste these deceptive links, they land on well-designed phishing pages created to steal login credentials.
E.g.: The link office365Scaffidips.azgcvhzauig.es. gives the impression that the user is dealing with a Microsoft subdomain. However, the last part of the web address: ‘azgcvhzauig.es’ is the attacker-owned phishing site.
Such evolving tactics highlight how cybercriminals constantly invent new methods to hide their threats.
According to Saravanan Mohankumar, Manager, Threat Analysis team, Barracuda, the firm sharing its threat intelligence findings: “The best defence… is a multilayered approach, with various levels of security that can spot, inspect and block unusual or unexpected activity. Solutions that include AI and machine-learning capabilities, both at the email gateway level and post-delivery, will ensure companies are well protected… Security measures should be complemented by active and regular security awareness training for employees.”

















