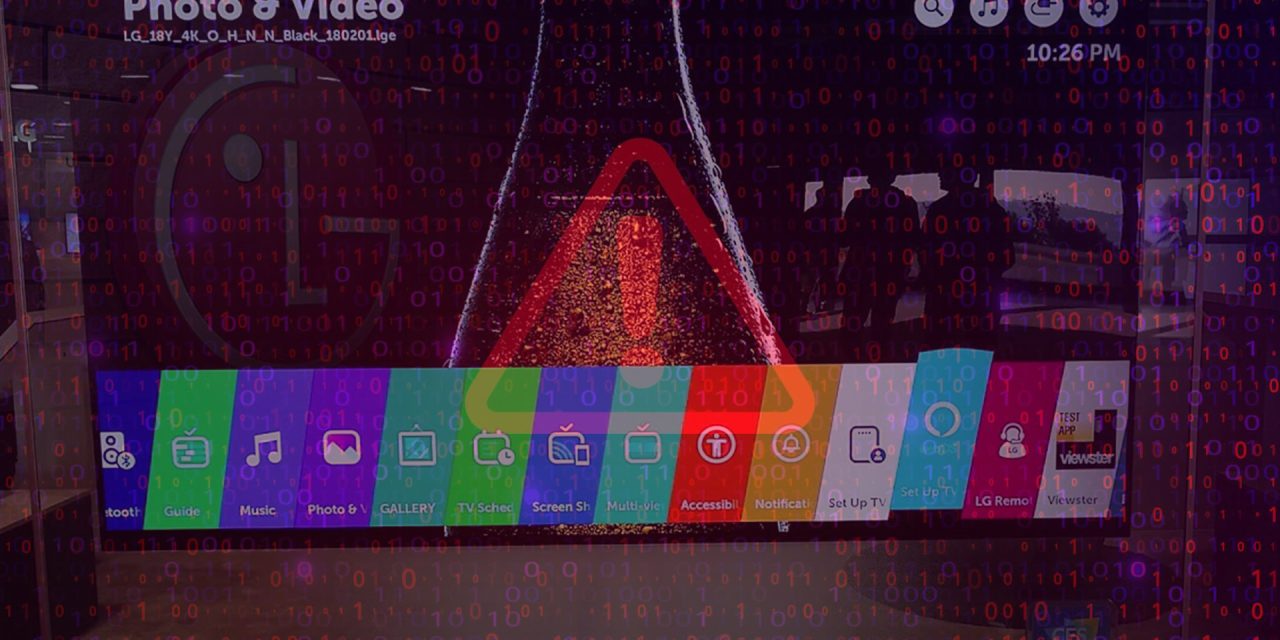
Smart TVs produced and sold in 2018 through 2022, if not updated regularly, could be harboring up to four vulnerabilities
On 9 April this year, cybersecurity researchers disclosed vulnerabilities affecting the proprietary TV operating system software of older LG TVs.
Specifically, the brand’s Linux-based operating system called WebOS was found to have harbored four vulnerabilities potentially affecting over 90,000 devices.
These vulnerabilities, found by Bitdefender researchers across versions 4 through 7, could have allowed unauthorized access and control, including authorization bypasses and command injection. Also, in early 2022, LG had renamed WebOS 6.0 to WebOS 22, throwing confusion into the mix.
Regardless, older LG TVs containing the vulnerabilities could have, instead of being local area network smart devices, been exposed to the internet, allowing possible malicious activities to occur. As different versions of WebOS are loaded and updated on various old models of such TVs, owners of old LG TVs should check if the model they own is affected, and then contact their LG service centers to get the OS patched if necessary.
According to Thomas Richards, Associate Principal Consultant, Synopsys Software Integrity Group, attackers could have used the affected Smart TV as a starting point to launch additional attacks against remote systems or hosts within the home network environment. Also, the owners’ personal data could have been exposed to compromise if the attacker(s) can gain administrative access to the TV.
Richards added: “Users should update their (affected) TV as soon as possible to remediate the vulnerabilities. In general, Smart TV owners should not have their TV directly connected to the internet. Keeping it linked through a router will reduce the likelihood of a compromise since remote attackers will not be able to reach it (easily). Enabling the automated update option on the TV will keep the TV up to date with vendor patches to remediate security risks.”