One Australian cybersecurity firm has released extensive details of its research on this type of attack on content producers.
According to one cybersecurity firm’s protection July–Sep 2023 ecosystem data, there has been a rapid increase in YouTube stream-jacking attacks.
Such attacks involve either taking full control of a targeted channel, or re-directing followers of that popular channel to another (fake) one run by cyber crooks.
The goal of YouTube stream-jacking is usually monetary: enticing followers of popular channels or personalities into sending cryptocurrency to get a 2X return on some fake investment scheme or product.
YouTube stream-jacking trends
The firm’s latest research metrics showed:
- The maximum number of subscribers of a hijacked account observed was nearly 10m. The top 10 accounts had nearly 37 million subscribers.
- The total number of subscribers from the top 10 hijacked channels was nearly 37m.
- The maximum number of views of a hijacked account observed was more than 3.6bn. The top 10 accounts had nearly 10.4bn views.
- Most hijacked channels featured a variation of the Tesla logo or the official logo; all top 10 hijacked accounts involved the Tesla brand.
- The median number of subscribers on a channel was 2,260.
- The median number of view counts on a channel was 211,820.
- The number of distinct channels found was 1,190; and there were 1,370 distinct livestream broadcasts.
- Some hijacked channels appeared to belong to governmental entities.
-
Channel spoofing: cybercriminals set up YouTube livestream pop-ups in followers’ feeds that promote generally the same content as the real channel. The pop-up livestreams are usually looped re-broadcasts that contain an embedded scam either via backlink or QR code to a phishing or fraudulent website. Due to the amount of livestream pop-ups observed, the operation is most likely automated.
Channel account takeover: In these attacks a YouTube channel owner is sent a fake email, usually offering a collaboration opportunity or notice of copyright infringement. The channel owner is encouraged to download a file included in the email that is actually malware. Once the file is opened, the malware steals data from the computer allowing the attacker to access YouTube account credentials, even bypassing extra security measures such as two-factor authentication (2FA). Once accessed, the real owner is usually locked out.
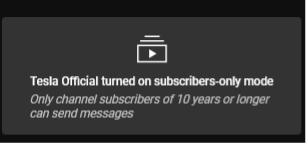
Targeted channels: The livestream content titles are broadly similar, and examples include A New Era for Tesla’s Model 3 – Live Reveal with Elon Musk! or SpaceX Launch Hughes JUPITER 3 Mission! Elon Musk gives update on Starship. The comment sections of detected malicious livestreams are often disabled, but accounts that enable comments only do so for subscribers of 10 or 15 years, preventing users aware of the scam from commenting and alerting others. A common detail of livestreams is that attackers embed a QR code in portions of the video that leads to a phishing or fraudulent website.
- Links propagated via hijacked YouTube channels promote similar and well-known scam involving sending any amount of cryptocurrency for promises to receive double the amount back.
- There have been instances in which the audio and video looped in the livestream are deepfakes of Elon Musk, through which the hackers try to promote the importance of crypto and any event promoted in the referenced links. The deepfakes are of high quality and may seem genuine to the average viewer.
- Some livestreams were view-boosted at the beginning of the broadcast, making it look more trustworthy. However, as soon as the view-boosting stopped, numerous fraudulent livestreams’ audience dropped to only one or two viewers.
- Even though there are enough occurrences of channels with low subscriber numbers, the median value of subscribers was close to 2,300, which indicates potential subscriber boosting.
- All the channels investigated were deduced to be created using automated software (phishing kits).
The findings by Bitdefender researchers also indicate that, in most cases analyzed, if the malicious activity is detected by YouTube, the actual channels are deleted altogether. This means that the legitimate owner of the channel will lose videos, playlists, views, subscribers, monetization and everything that goes beyond the YouTube channel itself while still being related — unless talks are undertaken with YouTube.













