Hackers have used legitimate system-sanctioned tools to steal data, and security software simply cannot be any the wiser!
Monitoring and management software help IT and network administrators to perform their everyday tasks, such as troubleshooting and providing employees with technical support. However, cybercriminals can also leverage these legitimate tools during cyberattacks on a company’s infrastructure. This software allows them to run processes on endpoints, access and extract sensitive information, bypassing various security controls aimed to detect malware.
Last year, almost a third (30%) of cyberattacks investigated by the Kaspersky Global Emergency Response team involved legitimate remote-management and administration tools. As a result, attackers were able to remain undetected for a longer period of time. For instance, continuous cyber-espionage attacks and theft of confidential data lasted a median period of 122 days, according to Kaspersky analytics.
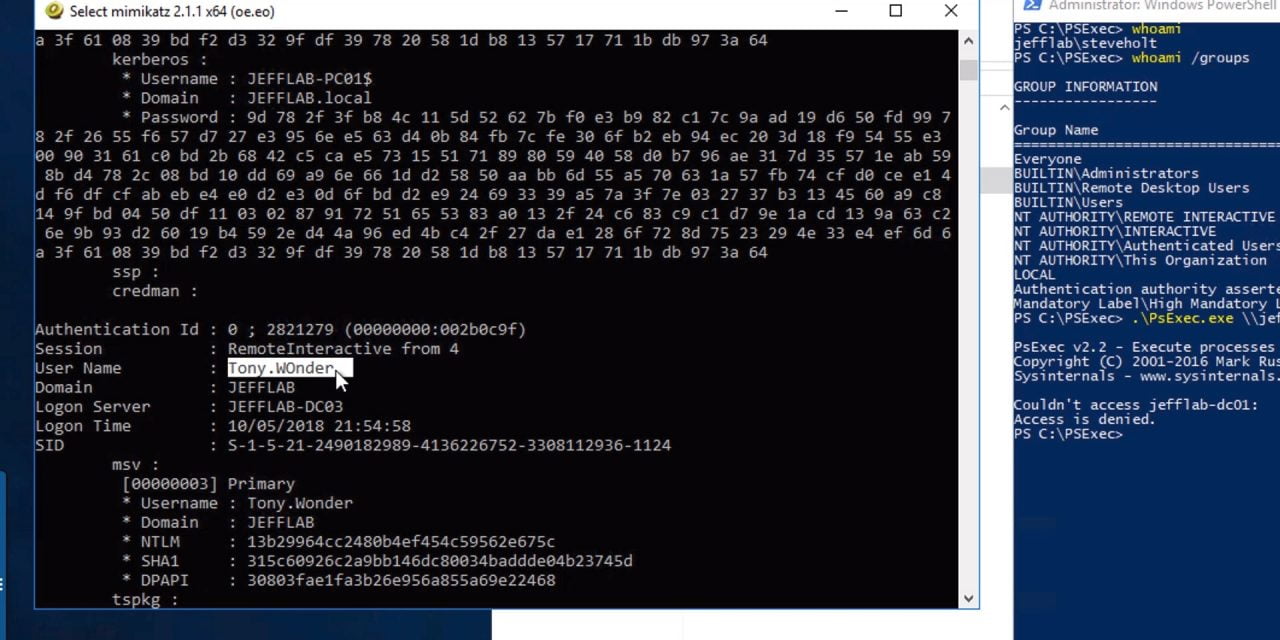
In total, the analysis of anonymized data from incident response (IR) cases showed that 18 legitimate tools had been abused by attackers for malicious purposes. The most widely-used tool was PowerShell (25% of cases). PsExec was leveraged in 22% of the attacks. This was followed by SoftPerfect Network Scanner (14%) which is used to retrieve information about network environments.
Evading detection through legitimate fronts
Security solutions typically sanction the actions of legitimate tools because these actions can be a regular system administrator task. The sanctioning of such tools has allowed attacks that lasted more for many months, allowing cybercriminals to collect huge amounts of sensitive data.
There are exceptions. Kaspersky experts noted that sometimes malicious actions with legitimate software can reveal their intent for detection rather quickly. For example, they are often used in a ransomware attack, and the damage is seen clearly. The median attack duration for short attacks was a day.
Commented Konstantin Sapronov, Kaspersky’s Head of Global Emergency Response: “Attackers widely use software which is developed for normal user activity, administrator tasks and system diagnostics. With these tools, attackers can gather information about corporate networks and then conduct lateral movement, change software and hardware settings or even carry out some form of malicious action. For example, they could use legitimate software to encrypt customer data. Legitimate software can also help attackers stay under the radar of security analysts, as they often detect the attack only after the damage has been done. It is not possible to exclude these tools for many reasons, however, properly-deployed logging and monitoring systems will help to detect suspicious activity in the network and complex attacks at earlier stages.”
Best practices to observe
To detect and react to such attacks in a timely manner, among other measures, organizations should consider implementing an endpoint detection and response (EDR) solution with a managed detection and response service (MDR).
This would comprise a more comprehensive solution that combines a fully automated multi-layered security product and a manual threat hunting service, according to Kaspersky.
Further, their researchers recommend the following measures:
- Restrict external IP addresses from accessing any remote management tools.
- Ensure that remote-control interfaces can only be accessed from a limited number of specific endpoints.
- Enforce a strict password policy for all IT systems, and deploy multi-factor authentication.
- Follow the principle of offering limited privileges to staff, and only granting high-privileged accounts to those who need the access to complete their tasks.