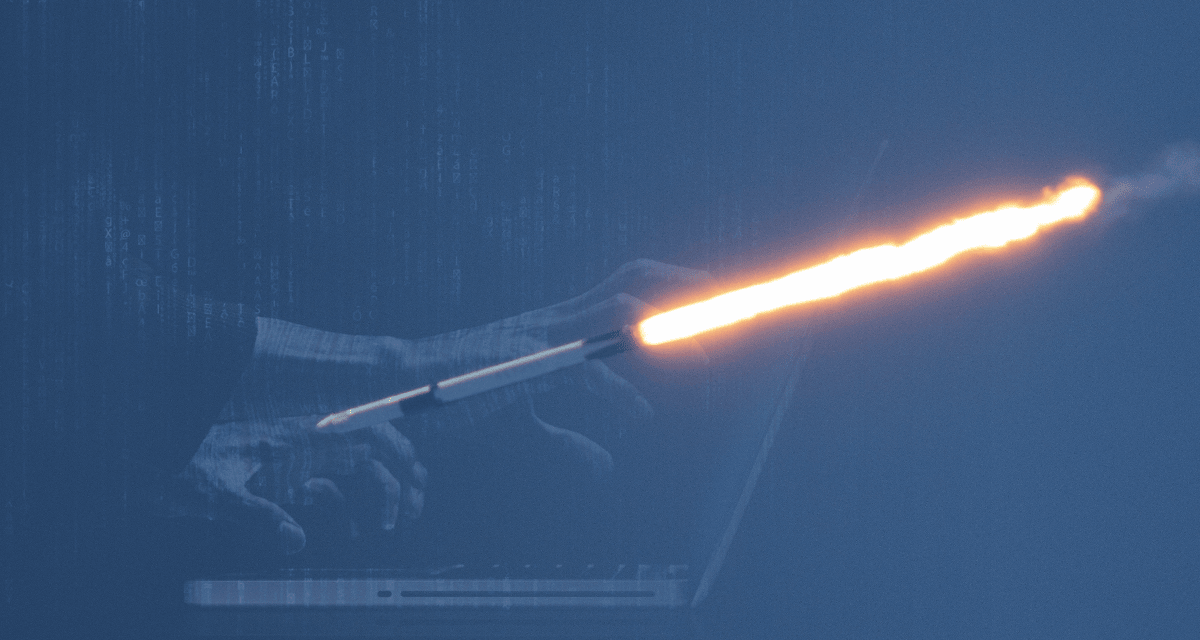
Amid elevated threat alerts, Iranian proxies and hacktivists are expected to target US-Israeli assets via DDoS campaigns and ‘wiper raids’.
Following the unprecedented digital offensive tied to US-Israeli military actions against Iran, cyber experts caution that the latter may launch cyber counterstrikes globally.
The joint US-Israeli operations — dubbed Operation Epic Fury by Washington — and Operation Roaring Lion by Jerusalem, had commenced on 28 February 28, 2026, blending airstrikes on IRGC sites in Tehran, Isfahan, and elsewhere with a massive cyber campaign.
This digital barrage has disrupted government sites, state media such as IRNA and Tasnim, and popular apps such as BadeSaba, a religious tool with millions of users among regime loyalists.
Reports cite Iran’s internet traffic crashing to 4% of normal, isolating the nation amid chaos, while Cloudflare reported near-zero web activity nationwide. Some observers have attributed this to combined cyberattacks and Tehran’s own restrictions echoing prior protest suppressions.
The assaults have incorporated DDoS floods, electronic warfare, and deep hacks into energy, aviation, and IRGC comms networks, hindering drone and missile launches. Even Iran’s “national internet” had buckled, plunging the regime into a communications void as missiles rained down. Some have labeled the assaults as history’s largest coordinated cyber hit, amplifying physical blows that had killed Supreme Leader Ali Khamenei and top officials.
Now, cybersecurity leaders predict swift Iranian payback, elevating their threat alerts, and warning that proxies and hacktivists could target US-Israeli military, infrastructure, finance, and civilian assets via DDoS, wipers, or data wipes. There have already been early signs of Iranian actors probing and DDoS-ing Israeli systems, while state-backed “wiper” raids are already underway.
Organizations are urged to bolster multi-factor authentication, patching exposures, and backup checks against likely phishing, brute-force, or destructive malware from IRGC-linked groups.
This cyber front risks broadening the conflict, as Iran’s battle-tested hackers — honed since early Shamoon attacks — eye retaliation without full military parity.
As opportunistic strikes could hit beyond combatants — as echoed by past escalations — cyber experts around the world are stressing heightened corporate cyber vigilance.