Anyone could soon target you for a chat session, using a new feature enabled by default in a popular collaboration tool.
While the world tries to plug every loophole and risk that could expose people to phishing attacks, one software giant is toying with just the opposite.
In a feature expected to roll out starting November 2025, users of Microsoft Teams will be able to initiate chats with anyone just by supplying an email address, without requiring the recipient to be a Teams user.
This update, aimed at enhancing seamless collaboration across platforms such as Android, desktop, iOS, Linux, and Mac, allows external guest users to join conversations via email invites under Microsoft Entra B2B Guest policies. While it aims to improve flexibility in communication, cybersecurity experts have raised alarms about significant security risks associated with the default-enabled setting.
The primary concern is the increased attack surface:
- By allowing external email-based chat initiations without prior validation or vetting, the feature opens avenues for phishing attacks and malware distribution. Malicious actors could send spoofed chat invites posing as trusted contacts or business partners, tricking employees into clicking harmful links, sharing credentials, or unknowingly exposing proprietary information.
- This vector is likened to OAuth phishing campaigns, which rely heavily on impersonation to harvest sensitive data. The risks are compounded because file exchanges within Teams may bypass traditional email security filters, raising the threat of ransomware or spyware infiltrations.
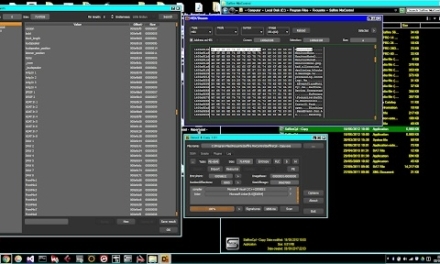
- Microsoft advises organizations to update internal policies and train staff on the new functionality. Administrators can mitigate risks by disabling the feature through PowerShell, using the TeamsMessagingPolicy attribute ‘UseB2BInvitesToAddExternalUsers’ set to false, thus restricting chats to vetted external users only.
Experts recommend additional security measures such as enforcing multi-factor authentication, conducting regular audits, and running comprehensive phishing awareness training.
Overall, while the new Teams feature offers improved external communication capabilities, the illogical choice to enable it by default will place the onus of security and privacy vigilance on users.