Recent Foxconn breach brings into focus the highly interconnected nature of global manufacturing supply chains, with an explosive growth in non-human identities.
The semiconductor industry is gearing up in APAC, with major operations in Taiwan, China, South Korea, Japan, Singapore, Vietnam, and Malaysia. It is also an increasingly high-stakes industry due to geopolitics and industry demand.
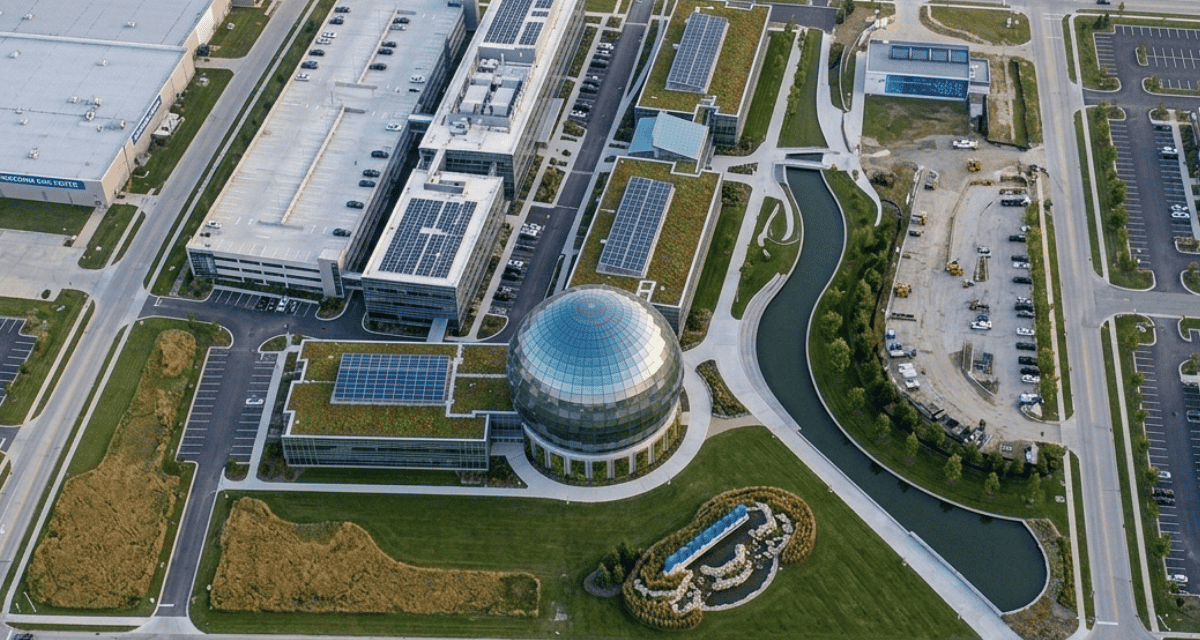
It has recently been widely reported that the Nitrogen ransomware group crippled Foxconn’s North American manufacturing facilities and forced a multi-day production standstill that required staff to resort to manual operations.
The attackers claim to have exfiltrated 8TB of sensitive data encompassing 11 million files, including confidential technical blueprints and schematics belonging to major partners like Google and Intel.
Takanori Nishiyama, Senior Vice President APAC, Keeper Security, commented: “The reported exfiltration of 8TB of data from Foxconn highlights the highly interconnected nature of the global manufacturing supply chain. When 11 million files, including technical blueprints and engineering schematics, are alleged to have been compromised, the competitive advantage and reputations of these organizations are placed at substantial risk.”
Multiple targets in manufacturing
Nishiyama explained “Modern manufacturing is no longer just about physical assembly; it is a complex digital ecosystem where a single point of failure can halt production across multiple continents.”
He pointed out that ransomware groups frequently target victims that provide a path into other organizations. “By compromising a primary supplier, attackers gain a vantage point into the sensitive schematics and project data of the entire tech sector.”
Relying on perimeter defenses is no longer sufficient in this threat landscape. Identity-related solutions such as Privileged Access Management (PAM) have become a foundational requirement for supply chain resilience.
Modern PAM platforms mitigate the risks associated with third-party vendors, standing access and overprivileged accounts that can provide attackers with unfettered access to an organization. PAM reduces the attacker’s window of opportunity by enabling Just-In-Time (JIT) access, which ensures privileges are granted only when necessary and revoked immediately after a task is completed.
AI and automation
The expansion of AI and automation in smart factories has also led to an explosion of Non-Human Identities (NHIs), such as service accounts and API keys.
“These identities often hold persistent, high-level privileges that blend into normal system activity, making them prime targets for lateral movement,” Nishiyama warned.
Keeper’s 20026 Global Insight Report found that 89% of IT and security leaders cite managing the growing number of human and non-human identities as a primary challenge.
“In an environment of Foxconn’s complexity, that challenge is acute, said Nishiyama. “Every remote contractor, service account and automated process represents a potential access point.”
What must be in place
Nishiyama emphasized that, without a unified zero-trust architecture to govern these identities, the entire supply chain remains vulnerable to lateral movement and data theft.
“The operational lesson is consistent regardless of how this incident unfolded,” he concluded. “Where IT infrastructure, operational technology and third-party supplier access intersect, the identity layer is the last reliable line of defense for high-value data.”
He added: “Privileged access must be time limited, verified and fully auditable at every layer, across human and service accounts, third-party access and the automated processes that increasingly sit at the heart of modern manufacturing.”