The campaign leverages generative models to script intrusions, extract configurations, obtain credentials, infiltrate networks and prepare systems for future ransomware operations.
In a recent threat report, Amazon announced that it had tracked a campaign between 11 January and 18 February 2026 where a malicious actor having “low-to-medium” technical skills had been “significantly augmented” by generative AI services had attempted to compromise more than 600 of its Fortinet firewalls across operations in at least 55 countries.
The Russian-speaking hacking group had reportedly used commercial AI tools, underscoring how AI is amplifying the impact of relatively low-skilled attackers.
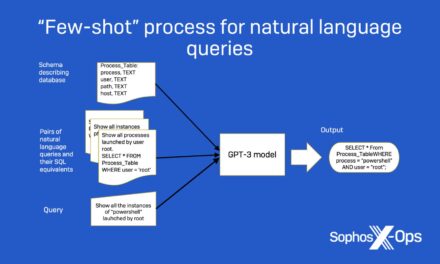
CJ Moses, the firm’s CISO, had described the operation as an “AI-powered assembly line for cybercrime,” with the attackers using at least two commercial large language model providers to generate scripts, design attack workflows and assist with post-compromise activities.
Rather than exploiting new software flaws in the firewall products, the hackers had focused on exposed management interfaces and weak, single-factor credentials on appliances reachable from the internet. Once the devices were compromised, the intruders exported full configuration files that contained SSL VPN credentials, administrator passwords and detailed network topology data, giving them a roadmap into victims’ internal environments. Using those credentials, the bad actors then broke into Windows domains, captured entire credential databases and attempted to reach backup systems — activity Amazon described as consistent with “pre‑ransomware” staging rather than immediate monetization.
The targeting appears largely opportunistic, hitting organizations whose firewall management ports were exposed and poorly secured, with clusters of victims in South Asia, Latin America, the Caribbean, West Africa, Northern Europe and South-east Asia.
When the attackers encountered stronger defenses or locked-down perimeter devices, they typically abandoned those targets and pivoted to easier ones, highlighting how AI allowed them to rapidly scan, script and iterate without needing deep expertise.
To blunt the campaign Amazon has shared indicators of compromise with partners and industry groups, and warned that AI-enhanced intrusion activity is likely to expand through 2026 as both sophisticated and novice actors adopt similar tooling.
Moses urged organizations to harden network edge devices by restricting management access, enforcing stronger authentication and rigorously monitoring for post-exploitation signs on firewalls and adjacent infrastructure.
https://www.bloomberg.com/news/articles/2026-02-20/hackers-used-ai-to-breach-600-firewalls-in-weeks-amazon-says