With a severity of 9.8, the vulnerability requires urgent patching that is already available.
A critical Zero Day vulnerability identified as CVE-2025-64446 has been actively exploited since October 2025, posing severe cybersecurity risks globally, according to various news reports.
This high-severity flaw, rated 9.8/10 on the CVSS scale, is found in the Fortinet FortiWeb Web Application Firewall, versions 8.0.1 and earlier.
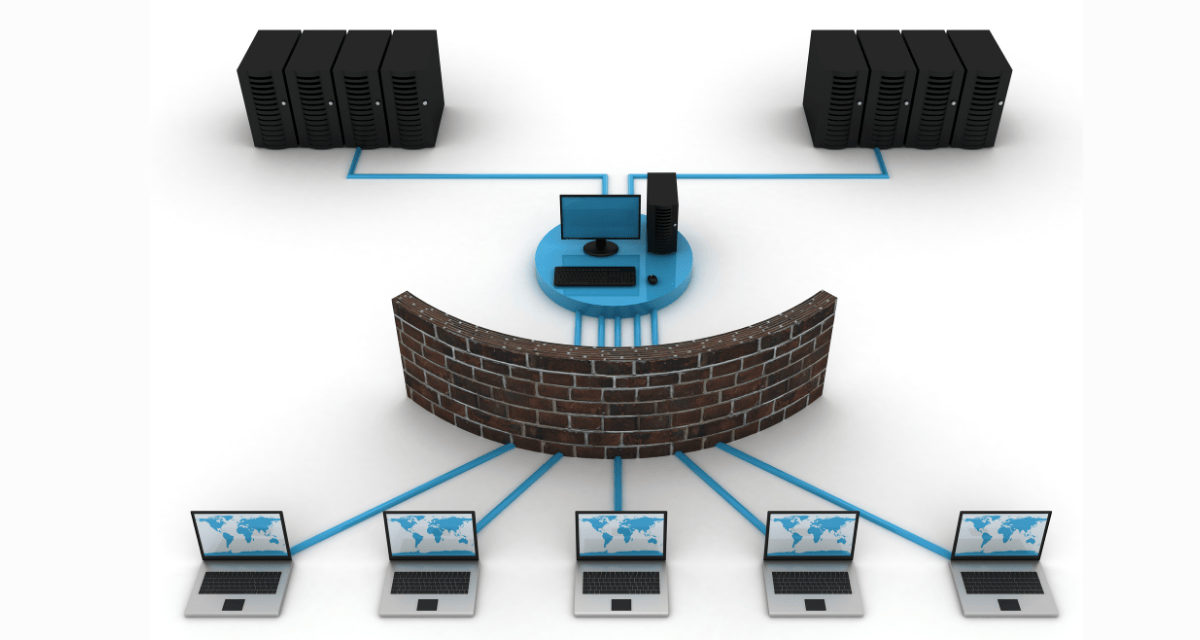
CVE-2025-64446 allows unauthenticated attackers to gain full administrative privileges on vulnerable devices, representing a significant compromise of network perimeter defenses. The vulnerability arises from a path traversal combined with an authentication bypass in the software’s request handling system:
- Attackers send specially crafted HTTP POST requests targeting the endpoint /api/v2.0/cmdb/system/admin%3f/../../../../../cgi-bin/fwbcgi.
This sequence bypasses normal authentication checks and grants attackers the ability to execute arbitrary administrative commands remotely. - A common exploitation method involves creating persistent unauthorized admin accounts with attacker-chosen usernames and passwords, enabling long-term control over devices without detection.
- The consequences of exploitation are grave. Attackers can disable or manipulate firewall rules, intercept, and modify application traffic, and use compromised FortiWeb devices as launch pads for lateral movement inside corporate networks. Due to the software’s integration with other Fortinet products, attackers may gain broader access to critical internal systems and sensitive data.
- Public proof-of-concept exploits surfaced quickly after initial detection in early October, with active exploitation reported worldwide including IP addresses in North America, Europe, and Asia.
The US Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2025-64446 to its Known Exploited Vulnerabilities catalog, emphasizing an urgent need for patching. Fortinet has responded by releasing version 8.0.2, which blocks exploitation attempts by returning HTTP 403 Forbidden responses, mitigating the vulnerability.
Organizations affected should immediately upgrade to version 8.0.2 or later, restrict internet exposure of management interfaces, and conduct thorough inspections for unknown administrative accounts or suspicious activity to detect prior compromise.
Monitoring logs for anomaly indicators and following Fortinet’s advisories are essential defensive measures. This incident underscores the urgency of maintaining rigorous patch management protocols and vigilant network monitoring to protect vital security infrastructure against emerging zero-day threats.