The retailchain was grappling with numerous cyber risks in its IT infrastructure until it upgraded to Zero Trust identity security
In the digital age, especially after year of rush digitalization due to the COVID-19 pandemic, the retail industry is facing increasingly severe cybersecurity challenges. One consumer retail chain, Heng Leong Hang of Taiwan, is acutely aware of the substantial cybersecurity exposure faced by hundreds of employees across its 70 stores.
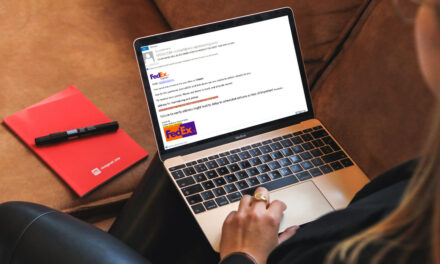
Threats faced so far have included theft of sensitive employee and customer data, as well as risks to point of sale systems. There was an urgent need to deliver improved management and control of its privileged accounts, as well as enhance security of its on-premises IT infrastructure and business services (including its website, e-commerce services, and AWS cloud resource environment).
According to the firm’s Head of Information, Timo Lu: “The size of our employee pool is our biggest challenge. To solve cybersecurity issues, we first need to address personnel and privileged access issues. This is why identity security is so crucial.” With that, Heng Leong Hang had to choose an identity security technology vendor to enhance how employee identities are authenticated and secured, as well as to lock down privileged access, a priority attack vector.
As a result, the company now has the right tools not only protect employees with highly privileged access and workstation endpoints, but a system that allows for automation of many security processes, enhancing employee work efficiency and reducing the burden of compliance. With the right levels of privilege control, human and machine identities are secured, and the identity lifecycle is monitored with continuous threat detection and prevention in a Zero Trust paradigm.
According to Edward Hsieh, Regional Director (North Asia), CyberArk, the identity security firm providing the enhancements: “We are delighted to have the opportunity to assist Heng Leong Hang in successfully strengthening its overall cybersecurity architecture, thereby protecting its employees, customers and business operations… (and providing) the necessary security foundation in an increasingly digitalized cloud-based business environment.”